Industrial Cybersecurity Market Size, Share & Trends Analysis Report by Security Type (Network Security, Endpoint Security, Application Security, Cloud Security, Wireless Security, Other Types), Component, Deployment Mode, Organization Size, Technology, Threat Type, Industry Protocol Security, End-users, and Geography (North America, Europe, Asia Pacific, Middle East, Africa, and South America) – Global Industry Data, Trends, and Forecasts, 2026–2035
|
|
|
Segmental Data Insights |
|
|
Demand Trends |
|
|
Competitive Landscape |
|
|
Strategic Development |
|
|
Future Outlook & Opportunities |
|
Industrial Cybersecurity Market Size, Share, and Growth
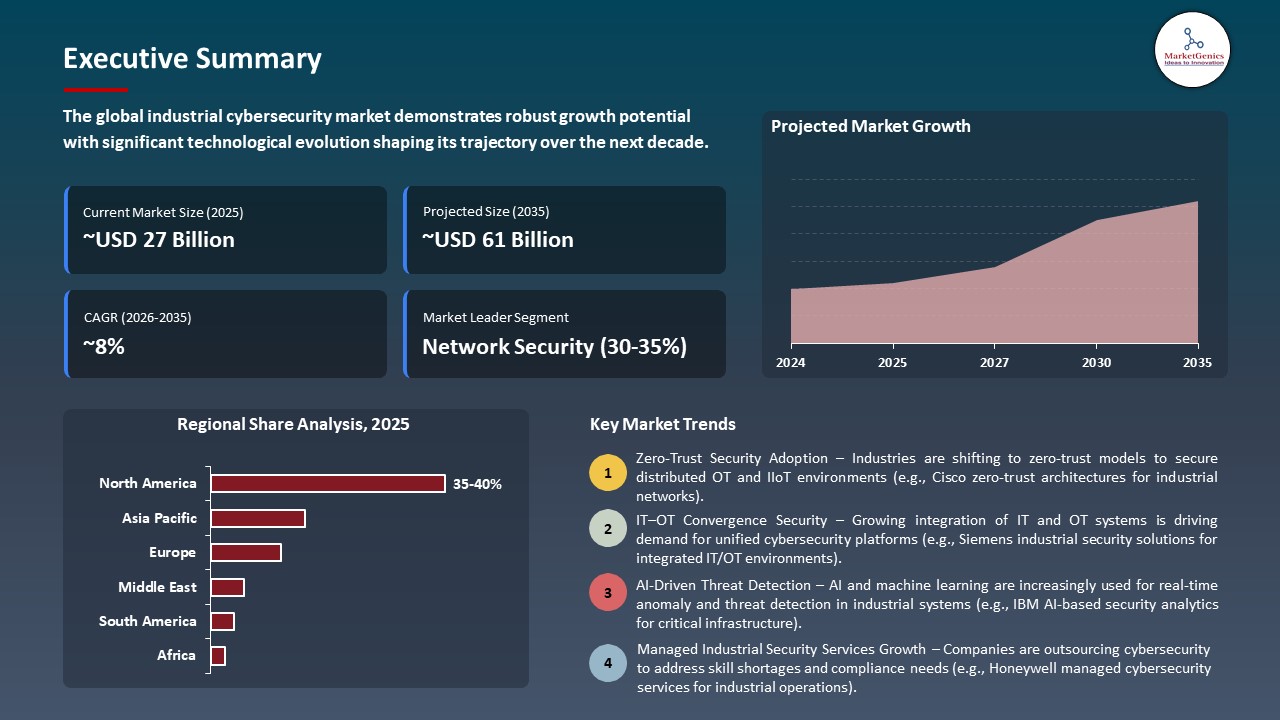
The global industrial cybersecurity market is witnessing strong growth, valued at USD 27.3 billion in 2025 and projected to reach USD 61.2 billion by 2035, expanding at a CAGR of 8.4% during the forecast period. Asia Pacific is the fastest-growing Industrial Cybersecurity market due to rapid industrialization, expanding adoption of Industry 4.0 and IIoT technologies, increasing cyber threats to critical infrastructure, and rising government initiatives to strengthen cybersecurity frameworks across manufacturing, energy, and utilities sectors.
Paul Smith, director of Honeywell Operational Technology (OT) Cybersecurity Engineering, said, “With increasingly significant threats and updated SEC reporting regulations requiring the disclosure of material cybersecurity incidents, industrial operators must act decisively to mitigate costly unplanned downtime and risks, including those linked to safety, Leveraging Zero Trust architecture and AI for security analysis can speed detection and enable smarter decision making and proactive defense in an increasingly complex digital landscape”.
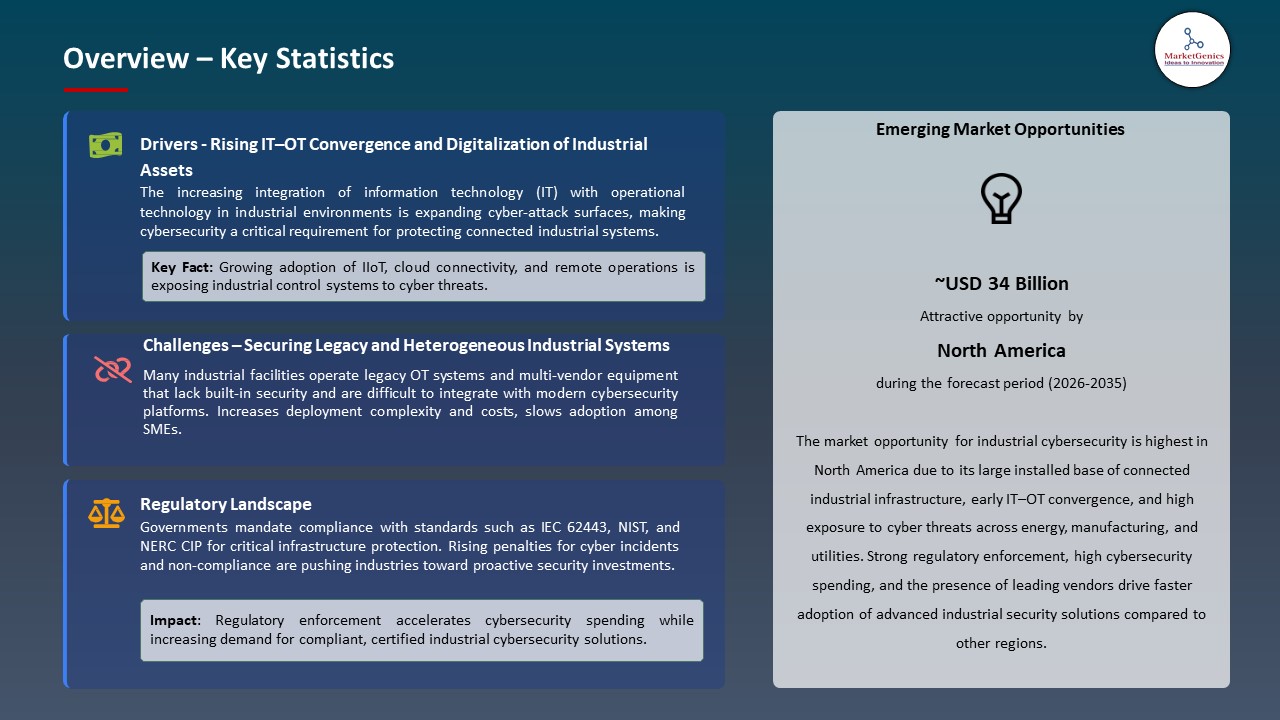
Cybersecurity is becoming a major concern among the industrial operators to protect operational resilience and business continuity. Having critical infrastructure and production processes vulnerable to cyberattacks, businesses seek to avoid unwanted downtime, breaches of data, and service disasters. Investing in cutting-edge threat detection, real-time monitoring, and IT/OT security infrastructure is a sure way to secure continuous operations, safeguard assets, and secure customer loyalty, that is, provoke a high demand in the industrial cybersecurity system in all industries.
The appearance of quantum-resistant security technologies is a great opportunity in the industrial cybersecurity market. The advancement of quantum computing is likely to jeopardize current encryption methods, necessitating the development of next-generation solutions to safeguard essential industrial infrastructure. The vendors of quantum-ready security platforms have the potential to future-proof the enterprise networks, safeguard operational data that is sensitive, and provide competitive advantage, motivating the industry to adopt sophisticated, future-oriented cybersecurity solutions.
Key adjacent opportunities for the industrial cybersecurity market include AI-driven threat intelligence, cloud and hybrid security services, managed detection and response, industrial IoT protection, and supply chain risk management. These areas complement core cybersecurity solutions, enabling enterprises to enhance resilience, reduce operational risk, and achieve proactive protection across IT and OT environments.
 Industrial Cybersecurity Market Dynamics and Trends
Industrial Cybersecurity Market Dynamics and Trends
Driver: Escalating Operational Technology Ransomware Attacks Fuel Industrial Cybersecurity Investments Worldwide
-
Industrial settings are experiencing a sudden surge of ransomware attacks that are specifically targeting the operational technology (OT) systems, such as industrial control systems, supervisory control and data acquisition systems, and connected production equipment. Such attacks are more and more based on legacy protocols, remote access ports, and IT-OT convergence points, which allows threat actors to interfere, compromise safety, and shut down production lines in the manufacturing, energy, and utilities industries. The increasing financial, operational, and reputational costs of the long-term non-availability and regulatory noncompliance are influencing industrial enterprises to invest in cybersecurity.
- Honeywell, in June 2025, pointed to a sudden and rapid increase in industrial cyber threats, noting that ransomware attacks increased 46% between Q4 2024 and Q1 2025 and that a credential-stealing trojan specific to OT was increasing by 3,000% in the same period. The examination of Honeywell global install base also demonstrated connective USB- and peripheral-based threats, which contributed to the pressing need of advanced OT cybersecurity solutions to avoid expensive and unplanned downtime in the key industrial processes.
- OT-specific threat detection, network segmentation, and incident response solutions are gaining demand, established as a strategic base of industrial resilience and continuity on cybersecurity.
Restraint: High Implementation and Integration Costs Constrain Industrial Cybersecurity Adoption by Manufacturers
-
Industrial cybersecurity implementations involve vast initial and continual investment, especially in a background of legacy operational technology that was not initially created with a connection or security in mind. To prevent security breaches, vendors will need to spend funds on special hardware, top security programs, ongoing system upgrades and expert services to conduct risk analysis, configuration and compliance. These expenses are also enhanced by the fact that custom-made solutions are required which will not interfere with the important production processes.
- Moreover, the implementation of cybersecurity systems in converged IT/OT systems requires human resources and prolonged implementation cycles, which raise the overall cost of operation. The smaller and mid-sized manufacturers find it hard to combat the need to justify return-on-investment because of the uncertainty of short-term financial returns, resulting in slow uptake.
- High implementation and integration still pose a major challenge, especially to cost-constrained industrial operators, which slows down market penetration even as cyber risk is increasing.
Opportunity: Expansion of AI-Driven Threat Intelligence Solutions Accelerates Industrial Cybersecurity Innovation
-
The current trend of introducing artificial intelligence and machine learning into industrial cybersecurity solutions poses a huge growth opportunity to the market. Threat intelligence based on AI facilitates real-time behavioral study, anomaly detection and predictable threat financial forecasting in sophisticated OT systems, in which customary rule-lacking security instruments appear to falter. These functions increase the visibility of industrial networks without causing as much false positive and operational interruptions.
- More Industrial systems are going to go online, so software vendors are going to use AI to provide automated incident response and continuous risk assessment that is specific to mission-critical functions. In February 2025, Trend Micro released the first proactive cybersecurity AI in the industry, Trend Cybertron, which is based on a dedicated large language model and allows prediction of potential risks, attack-path models, and automatic threat prevention in both enterprise and industrial environments.
- This change generates powerful solution differentiation, controlled security service, and scalable cybersecurity products, in line with Industry 4.0 and smart manufacturing efforts.
Key Trend: Increased Regulatory and Supply Chain Cybersecurity Oversight Driving Comprehensive Industrial Security Investments
- Industrial enterprises are increasingly under regulatory scrutiny and are increasingly being expected to not only secure internal operations, but also long supply chains that back important infrastructure. Governments and regulatory authorities are setting more stringent cybersecurity disclosure regulations, incident reporting regulations, and compliance structures, which force the manufacturers to enhance visibility, risk management and governance in the interrelated OT and IT systems.
- Simultaneously, the escalating questions on the vulnerability of third parties and supplier-led cyber threats are also compelling industrial operators to implement standard security controls, ongoing monitoring, and vendor risk assessment.
- Notably, the production shutdown of Jaguar Land Rover and disruptive ransomware attacks of major airports in Europe indicated that European leaders in the industrial sector were responding to the NIS2 directive by accelerating investments in OT cybersecurity in October 2025. NIS2 served as an essential step in raising OT security to the board level, compelling businesses to increase the supply-chain visibility, executive responsibility and real-time governance structures to improve the resilience of their operations and competitive status.
- This move is making integrated cybersecurity solutions supporting compliance, secure system updates, and end-to-end protection increasingly sought after, and regulatory and supply chain control seems to be a key driver of industrial cybersecurity investment in the long term.
 Industrial-Cybersecurity-Market Analysis and Segmental Data
Industrial-Cybersecurity-Market Analysis and Segmental Data
Network Security Dominate Global Industrial Cybersecurity Market
-
The network security segment continues to dominate the global industrial cybersecurity market due to its critical role in protecting complex IT and OT infrastructures from escalating cyber threats. Industrial networks, including SCADA systems, programmable logic controllers (PLCs), and connected IoT devices, are increasingly targeted by ransomware, malware, and advanced persistent threats, making robust network security solutions essential.
- Enterprises are now focusing on firewalls, intrusion detection and prevention systems (IDPS), secure remote access and network segmentation technology to ensure continuity in operations. Network security solutions aiming at industrial customers are becoming more and more susceptible to threat intelligence, AI-driven visibility and automated protection.
- In January 2025, Fortinet is being named the Overall Leader in the Westlands Advisory IT/OT Network Protection Platform Navigator report the third in a row. Fortinet OT Security Platform was also mentioned as offering end-to-end network segmentation, OT asset visibility, advanced threat protection, and AI-driven security services, which allow IT/OT convergence to be achieved securely and operational resilience to be improved.
- Network security remains the backbone of industrial cybersecurity, as industries are embracing digitalization and remote connections, driving further growth in the market and technological progress.
North America Leads Global Industrial Cybersecurity Market Demand
-
North America remains the leading region in the global industrial cybersecurity market, driven by rapid adoption of advanced technologies, high digitalization across industrial sectors, and a strong regulatory environment emphasizing cyber risk management. The region hosts a large number of critical infrastructure facilities, including energy, manufacturing, and transportation networks, which increasingly rely on connected OT and IT systems, making cybersecurity a top priority.
- North American enterprises are devoting significant investments to comprehensive cybersecurity services, such as network security, endpoint protection, threat intelligence, and AI-based monitoring to ensure operations are not targeted by more advanced cyberattacks like ransomware, malware, and phishing campaigns. Besides this, increased regulatory controls and compliance demands force organizations to develop strong security frameworks, which also add to the market leadership in the region.
- North America’s dominance in industrial cybersecurity solutions is bolstered by the prevalence of cybersecurity vendors, technological innovation, and awareness of cyber risk among industrial operators, making it the most mature and rapidly developing market in this field globally.
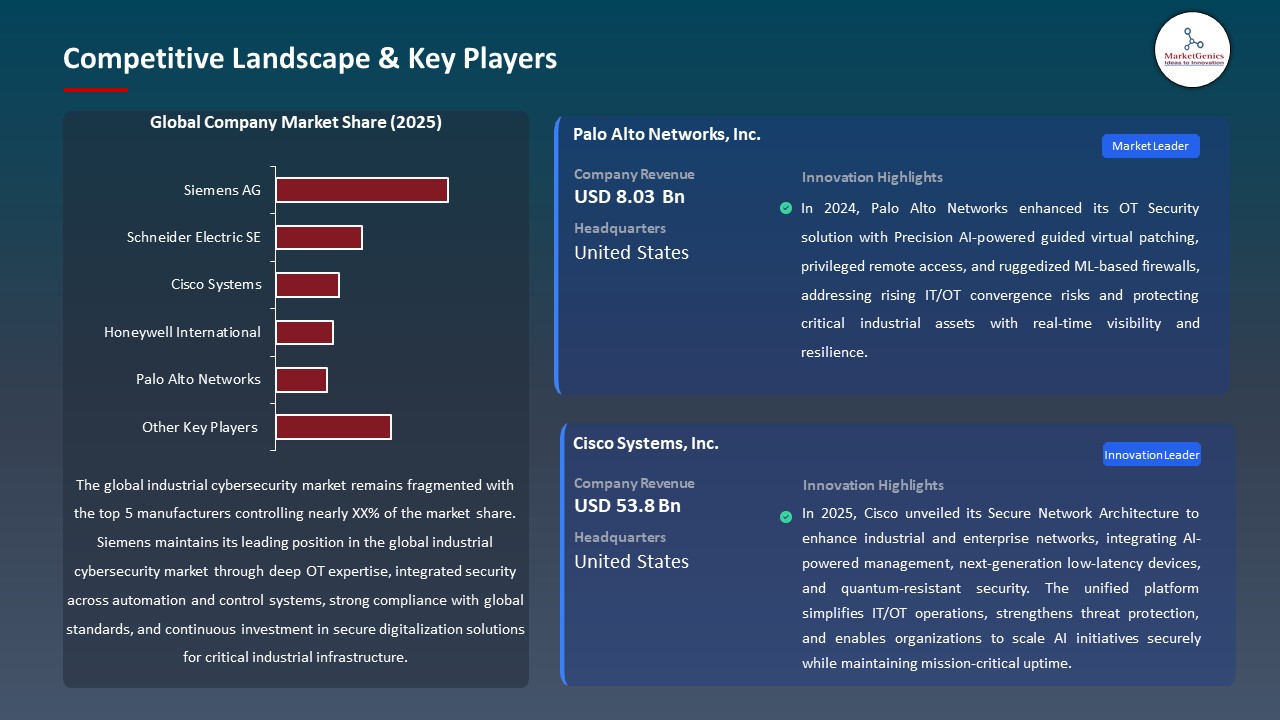
Industrial-Cybersecurity-Market Ecosystem
The global industrial cybersecurity market is fragmented, with leading players including Siemens, Schneider Electric, Cisco Systems, Honeywell International, and Palo Alto Networks. These companies secure strong market positions through continuous research and development, innovation in hardware and software security solutions, and expertise in integrating IT and OT systems for real-time industrial operations. Their leadership is further reinforced by long-standing relationships with manufacturers, energy utilities, transportation networks, and smart infrastructure operators, alongside extensive global distribution channels and adherence to strict regulatory and cybersecurity standards.
The industrial cybersecurity value chain spans the design and development of secure OT and IT devices, deployment of AI-driven monitoring platforms, integration with IoT, cloud, and edge solutions, and customized implementation for specific industrial environments. Post-deployment support—including continuous monitoring, maintenance, updates, and employee training—ensures operational efficiency, real-time threat visibility, and regulatory compliance while enabling smooth adoption of advanced cybersecurity solutions.
High entry barriers in the market stem from significant capital investment, advanced technical expertise, and strict compliance requirements. Continuous innovations, including AI-based threat intelligence, predictive analytics, and secure hybrid IT/OT architectures, drive differentiation, improve operational resilience, and sustain long-term global market growth.
 Recent Development and Strategic Overview:
Recent Development and Strategic Overview:
-
In October 2025, Palo Alto Networks launched its Strata Network Security Platform and Prisma AIRS 2.0, introducing AI-driven, quantum-ready network security. These solutions unify defenses, protect browser-based workspaces, and secure the entire AI ecosystem across applications, agents, models, and data, enabling enterprises to adapt to emerging threats while maintaining operational agility.
- In June 2025, Cisco unveiled its Secure Network Architecture to enhance industrial and enterprise networks, integrating AI-powered management, next-generation low-latency devices, and quantum-resistant security. The unified platform simplifies IT/OT operations, strengthens threat protection, and enables organizations to scale AI initiatives securely while maintaining mission-critical uptime.
Report Scope
|
Detail |
|
|
Market Size in 2025 |
USD 27.3 Bn |
|
Market Forecast Value in 2035 |
USD 61.2 Bn |
|
Growth Rate (CAGR) |
8.4% |
|
Forecast Period |
2026 – 2035 |
|
Historical Data Available for |
2021 – 2024 |
|
Market Size Units |
US$ Billion for Value |
|
Report Format |
Electronic (PDF) + Excel |
|
North America |
Europe |
Asia Pacific |
Middle East |
Africa |
South America |
|
|
|
|
|
|
|
Companies Covered |
|||||
|
|
|
|
|
|
Industrial-Cybersecurity-Market Segmentation and Highlights
|
Segment |
Sub-segment |
|
Industrial Cybersecurity Market, By Security Type |
|
|
Industrial Cybersecurity Market, By Component |
|
|
Industrial Cybersecurity Market, By Deployment Mode |
|
|
Industrial Cybersecurity Market, By Organization Size |
|
|
Industrial Cybersecurity Market, By Technology |
|
|
Industrial Cybersecurity Market, By Threat Type |
|
|
Industrial Cybersecurity Market, By Industry Protocol Security |
|
|
Industrial Cybersecurity Market, By End-users |
|
Frequently Asked Questions
Table of Contents
- 1. Research Methodology and Assumptions
- 1.1. Definitions
- 1.2. Research Design and Approach
- 1.3. Data Collection Methods
- 1.4. Base Estimates and Calculations
- 1.5. Forecasting Models
- 1.5.1. Key Forecast Factors & Impact Analysis
- 1.6. Secondary Research
- 1.6.1. Open Sources
- 1.6.2. Paid Databases
- 1.6.3. Associations
- 1.7. Primary Research
- 1.7.1. Primary Sources
- 1.7.2. Primary Interviews with Stakeholders across Ecosystem
- 2. Executive Summary
- 2.1. Global Industrial Cybersecurity Market Outlook
- 2.1.1. Industrial Cybersecurity Market Size Value (US$ Bn), and Forecasts, 2021-2035
- 2.1.2. Compounded Annual Growth Rate Analysis
- 2.1.3. Growth Opportunity Analysis
- 2.1.4. Segmental Share Analysis
- 2.1.5. Geographical Share Analysis
- 2.2. Market Analysis and Facts
- 2.3. Supply-Demand Analysis
- 2.4. Competitive Benchmarking
- 2.5. Go-to- Market Strategy
- 2.5.1. Customer/ End-use Industry Assessment
- 2.5.2. Growth Opportunity Data, 2026-2035
- 2.5.2.1. Regional Data
- 2.5.2.2. Country Data
- 2.5.2.3. Segmental Data
- 2.5.3. Identification of Potential Market Spaces
- 2.5.4. GAP Analysis
- 2.5.5. Potential Attractive Price Points
- 2.5.6. Prevailing Market Risks & Challenges
- 2.5.7. Preferred Sales & Marketing Strategies
- 2.5.8. Key Recommendations and Analysis
- 2.5.9. A Way Forward
- 2.1. Global Industrial Cybersecurity Market Outlook
- 3. Industry Data and Premium Insights
- 3.1. Global Automation & Process Control Industry Overview, 2025
- 3.1.1. Automation & Process Control Industry Ecosystem Analysis
- 3.1.2. Key Trends for Automation & Process Control Industry
- 3.1.3. Regional Distribution for Automation & Process Control Industry
- 3.2. Supplier Customer Data
- 3.3. Technology Roadmap and Developments
- 3.4. Trade Analysis
- 3.4.1. Import & Export Analysis, 2025
- 3.4.2. Top Importing Countries
- 3.4.3. Top Exporting Countries
- 3.5. Trump Tariff Impact Analysis
- 3.5.1. Manufacturer
- 3.5.1.1. Based on the component & Raw material
- 3.5.2. Supply Chain
- 3.5.3. End Consumer
- 3.5.1. Manufacturer
- 3.6. Raw Material Analysis
- 3.1. Global Automation & Process Control Industry Overview, 2025
- 4. Market Overview
- 4.1. Market Dynamics
- 4.1.1. Drivers
- 4.1.1.1. Rising frequency and sophistication of cyberattacks on industrial infrastructure.
- 4.1.1.2. Increasing digitalization and adoption of IoT/Industry 4.0 technologies.
- 4.1.1.3. Stringent regulatory compliance and data protection requirements.
- 4.1.2. Restraints
- 4.1.2.1. High implementation and operational costs of cybersecurity solutions.
- 4.1.2.2. Shortage of skilled cybersecurity professionals in the industrial sector.
- 4.1.1. Drivers
- 4.2. Key Trend Analysis
- 4.3. Regulatory Framework
- 4.3.1. Key Regulations, Norms, and Subsidies, by Key Countries
- 4.3.2. Tariffs and Standards
- 4.3.3. Impact Analysis of Regulations on the Market
- 4.4. Ecosystem Analysis
- 4.5. Porter’s Five Forces Analysis
- 4.6. PESTEL Analysis
- 4.7. Global Industrial Cybersecurity Market Demand
- 4.7.1. Historical Market Size – Value (US$ Bn), 2020-2024
- 4.7.2. Current and Future Market Size – Value (US$ Bn), 2026–2035
- 4.7.2.1. Y-o-Y Growth Trends
- 4.7.2.2. Absolute $ Opportunity Assessment
- 4.1. Market Dynamics
- 5. Competition Landscape
- 5.1. Competition structure
- 5.1.1. Fragmented v/s consolidated
- 5.2. Company Share Analysis, 2025
- 5.2.1. Global Company Market Share
- 5.2.2. By Region
- 5.2.2.1. North America
- 5.2.2.2. Europe
- 5.2.2.3. Asia Pacific
- 5.2.2.4. Middle East
- 5.2.2.5. Africa
- 5.2.2.6. South America
- 5.3. Product Comparison Matrix
- 5.3.1. Specifications
- 5.3.2. Market Positioning
- 5.3.3. Pricing
- 5.1. Competition structure
- 6. Global Industrial Cybersecurity Market Analysis, by Security Type
- 6.1. Key Segment Analysis
- 6.2. Industrial Cybersecurity Market Size Value (US$ Bn), Analysis, and Forecasts, by Security Type, 2021-2035
- 6.2.1. Network Security
- 6.2.1.1. Firewalls
- 6.2.1.2. Intrusion Detection Systems (IDS)
- 6.2.1.3. Intrusion Prevention Systems (IPS)
- 6.2.1.4. Virtual Private Networks (VPN)
- 6.2.1.5. Network Access Control (NAC)
- 6.2.1.6. Others
- 6.2.2. Endpoint Security
- 6.2.2.1. Antivirus/Anti-malware
- 6.2.2.2. Endpoint Detection and Response (EDR)
- 6.2.2.3. Device Control
- 6.2.2.4. Application Whitelisting
- 6.2.2.5. Others
- 6.2.3. Application Security
- 6.2.3.1. Secure Coding
- 6.2.3.2. Application Scanning
- 6.2.3.3. Runtime Application Self-Protection (RASP)
- 6.2.3.4. Web Application Firewalls (WAF)
- 6.2.3.5. Others
- 6.2.4. Cloud Security
- 6.2.4.1. Cloud Access Security Brokers (CASB)
- 6.2.4.2. Cloud Workload Protection
- 6.2.4.3. Cloud Security Posture Management
- 6.2.4.4. Others
- 6.2.5. Wireless Security
- 6.2.5.1. Wi-Fi Security
- 6.2.5.2. Bluetooth Security
- 6.2.5.3. Cellular Security
- 6.2.5.4. Others
- 6.2.6. Other Types
- 6.2.1. Network Security
- 7. Global Industrial Cybersecurity Market Analysis, by Component
- 7.1. Key Segment Analysis
- 7.2. Industrial Cybersecurity Market Size Value (US$ Bn), Analysis, and Forecasts, by Component, 2021-2035
- 7.2.1. Solutions
- 7.2.1.1. Hardware-based Solutions
- 7.2.1.2. Software-based Solutions
- 7.2.1.3. Integrated Solutions
- 7.2.2. Services
- 7.2.2.1. Professional Services
- 7.2.2.1.1. Risk Assessment
- 7.2.2.1.2. Consulting
- 7.2.2.1.3. Integration and Implementation
- 7.2.2.1.4. Training and Education
- 7.2.2.2. Managed Services
- 7.2.2.2.1. Monitoring Services
- 7.2.2.2.2. Incident Response Services
- 7.2.2.2.3. Threat Intelligence Services
- 7.2.2.2.4. Others
- 7.2.2.1. Professional Services
- 7.2.1. Solutions
- 8. Global Industrial Cybersecurity Market Analysis, by Deployment Model
- 8.1. Key Segment Analysis
- 8.2. Industrial Cybersecurity Market Size Value (US$ Bn), Analysis, and Forecasts, by Deployment Model, 2021-2035
- 8.2.1. On-premises
- 8.2.1.1. Traditional Infrastructure
- 8.2.1.2. Private Data Centers
- 8.2.2. Cloud-based
- 8.2.3. Edge Deployment
- 8.2.1. On-premises
- 9. Global Industrial Cybersecurity Market Analysis, by Organization Size
- 9.1. Key Segment Analysis
- 9.2. Industrial Cybersecurity Market Size Value (US$ Bn), Analysis, and Forecasts, by Organization Size, 2021-2035
- 9.2.1. Large Enterprises
- 9.2.2. Small and Medium Enterprises (SMEs)
- 10. Global Industrial Cybersecurity Market Analysis, by Technology
- 10.1. Key Segment Analysis
- 10.2. Industrial Cybersecurity Market Size Value (US$ Bn), Analysis, and Forecasts, by Technology, 2021-2035
- 10.2.1. Industrial Control Systems (ICS) Security
- 10.2.1.1. SCADA Security
- 10.2.1.2. DCS Security
- 10.2.1.3. PLC Security
- 10.2.1.4. HMI Security
- 10.2.1.5. Others
- 10.2.2. Operational Technology (OT) Security
- 10.2.3. Internet of Things (IoT) Security
- 10.2.3.1. Industrial IoT (IIoT) Security
- 10.2.3.2. Connected Device Security
- 10.2.4. Artificial Intelligence and Machine Learning
- 10.2.5. Blockchain-based Security
- 10.2.6. Identity and Access Management (IAM)
- 10.2.7. Security Information and Event Management (SIEM)
- 10.2.8. Data Loss Prevention (DLP)
- 10.2.9. Others
- 10.2.1. Industrial Control Systems (ICS) Security
- 11. Global Industrial Cybersecurity Market Analysis, by Threat Type
- 11.1. Key Segment Analysis
- 11.2. Industrial Cybersecurity Market Size Value (US$ Bn), Analysis, and Forecasts, by Threat Type, 2021-2035
- 11.2.1. Malware
- 11.2.1.1. Ransomware
- 11.2.1.2. Trojans
- 11.2.1.3. Worms
- 11.2.1.4. Viruses
- 11.2.1.5. Others
- 11.2.2. Phishing and Social Engineering
- 11.2.3. Distributed Denial of Service (DDoS)
- 11.2.4. Advanced Persistent Threats (APT)
- 11.2.5. Insider Threats
- 11.2.6. Zero-Day Exploits
- 11.2.7. Supply Chain Attacks
- 11.2.8. Others
- 11.2.1. Malware
- 12. Global Industrial Cybersecurity Market Analysis, by Industry Protocol Security
- 12.1. Key Segment Analysis
- 12.2. Industrial Cybersecurity Market Size Value (US$ Bn), Analysis, and Forecasts, by Industry Protocol Security, 2021-2035
- 12.2.1. Modbus Security
- 12.2.2. DNP3 Security
- 12.2.3. EtherNet/IP Security
- 12.2.4. PROFINET Security
- 12.2.5. OPC UA Security
- 12.2.6. BACnet Security
- 12.2.7. Others
- 13. Global Industrial Cybersecurity Market Analysis and Forecasts, by End-users
- 13.1. Key Findings
- 13.2. Industrial Cybersecurity Market Size Value (US$ Bn), Analysis, and Forecasts, by End-users, 2021-2035
- 13.2.1. Energy & Power
- 13.2.2. Manufacturing
- 13.2.3. Oil & Gas
- 13.2.4. Chemical & Petrochemical
- 13.2.5. Water & Wastewater
- 13.2.6. Transportation & Logistics
- 13.2.7. Building Automation
- 13.2.8. Pharmaceutical & Healthcare
- 13.2.9. Utilities
- 13.2.10. Critical Infrastructure
- 13.2.11. Other End-users
- 14. Global Industrial Cybersecurity Market Analysis and Forecasts, by Region
- 14.1. Key Findings
- 14.2. Industrial Cybersecurity Market Size Value (US$ Bn), Analysis, and Forecasts, by Region, 2021-2035
- 14.2.1. North America
- 14.2.2. Europe
- 14.2.3. Asia Pacific
- 14.2.4. Middle East
- 14.2.5. Africa
- 14.2.6. South America
- 15. North America Industrial Cybersecurity Market Analysis
- 15.1. Key Segment Analysis
- 15.2. Regional Snapshot
- 15.3. North America Industrial Cybersecurity Market Size Value (US$ Bn), Analysis, and Forecasts, 2021-2035
- 15.3.1. Security Type
- 15.3.2. Component
- 15.3.3. Deployment Mode
- 15.3.4. Organization Size
- 15.3.5. Technology
- 15.3.6. Threat Type
- 15.3.7. Industry Protocol Security
- 15.3.8. End-users
- 15.3.9. Country
- 15.3.9.1. USA
- 15.3.9.2. Canada
- 15.3.9.3. Mexico
- 15.4. USA Industrial Cybersecurity Market
- 15.4.1. Country Segmental Analysis
- 15.4.2. Security Type
- 15.4.3. Component
- 15.4.4. Deployment Mode
- 15.4.5. Organization Size
- 15.4.6. Technology
- 15.4.7. Threat Type
- 15.4.8. Industry Protocol Security
- 15.4.9. End-users
- 15.5. Canada Industrial Cybersecurity Market
- 15.5.1. Country Segmental Analysis
- 15.5.2. Security Type
- 15.5.3. Component
- 15.5.4. Deployment Mode
- 15.5.5. Organization Size
- 15.5.6. Technology
- 15.5.7. Threat Type
- 15.5.8. Industry Protocol Security
- 15.5.9. End-users
- 15.6. Mexico Industrial Cybersecurity Market
- 15.6.1. Country Segmental Analysis
- 15.6.2. Security Type
- 15.6.3. Component
- 15.6.4. Deployment Mode
- 15.6.5. Organization Size
- 15.6.6. Technology
- 15.6.7. Threat Type
- 15.6.8. Industry Protocol Security
- 15.6.9. End-users
- 16. Europe Industrial Cybersecurity Market Analysis
- 16.1. Key Segment Analysis
- 16.2. Regional Snapshot
- 16.3. Europe Industrial Cybersecurity Market Size Value (US$ Bn), Analysis, and Forecasts, 2021-2035
- 16.3.1. Security Type
- 16.3.2. Component
- 16.3.3. Deployment Mode
- 16.3.4. Organization Size
- 16.3.5. Technology
- 16.3.6. Threat Type
- 16.3.7. Industry Protocol Security
- 16.3.8. End-users
- 16.3.9. Country
- 16.3.9.1. Germany
- 16.3.9.2. United Kingdom
- 16.3.9.3. France
- 16.3.9.4. Italy
- 16.3.9.5. Spain
- 16.3.9.6. Netherlands
- 16.3.9.7. Nordic Countries
- 16.3.9.8. Poland
- 16.3.9.9. Russia & CIS
- 16.3.9.10. Rest of Europe
- 16.4. Germany Industrial Cybersecurity Market
- 16.4.1. Country Segmental Analysis
- 16.4.2. Security Type
- 16.4.3. Component
- 16.4.4. Deployment Mode
- 16.4.5. Organization Size
- 16.4.6. Technology
- 16.4.7. Threat Type
- 16.4.8. Industry Protocol Security
- 16.4.9. End-users
- 16.5. United Kingdom Industrial Cybersecurity Market
- 16.5.1. Country Segmental Analysis
- 16.5.2. Security Type
- 16.5.3. Component
- 16.5.4. Deployment Mode
- 16.5.5. Organization Size
- 16.5.6. Technology
- 16.5.7. Threat Type
- 16.5.8. Industry Protocol Security
- 16.5.9. End-users
- 16.6. France Industrial Cybersecurity Market
- 16.6.1. Country Segmental Analysis
- 16.6.2. Security Type
- 16.6.3. Component
- 16.6.4. Deployment Mode
- 16.6.5. Organization Size
- 16.6.6. Technology
- 16.6.7. Threat Type
- 16.6.8. Industry Protocol Security
- 16.6.9. End-users
- 16.7. Italy Industrial Cybersecurity Market
- 16.7.1. Country Segmental Analysis
- 16.7.2. Security Type
- 16.7.3. Component
- 16.7.4. Deployment Mode
- 16.7.5. Organization Size
- 16.7.6. Technology
- 16.7.7. Threat Type
- 16.7.8. Industry Protocol Security
- 16.7.9. End-users
- 16.8. Spain Industrial Cybersecurity Market
- 16.8.1. Country Segmental Analysis
- 16.8.2. Security Type
- 16.8.3. Component
- 16.8.4. Deployment Mode
- 16.8.5. Organization Size
- 16.8.6. Technology
- 16.8.7. Threat Type
- 16.8.8. Industry Protocol Security
- 16.8.9. End-users
- 16.9. Netherlands Industrial Cybersecurity Market
- 16.9.1. Country Segmental Analysis
- 16.9.2. Security Type
- 16.9.3. Component
- 16.9.4. Deployment Mode
- 16.9.5. Organization Size
- 16.9.6. Technology
- 16.9.7. Threat Type
- 16.9.8. Industry Protocol Security
- 16.9.9. End-users
- 16.10. Nordic Countries Industrial Cybersecurity Market
- 16.10.1. Country Segmental Analysis
- 16.10.2. Security Type
- 16.10.3. Component
- 16.10.4. Deployment Mode
- 16.10.5. Organization Size
- 16.10.6. Technology
- 16.10.7. Threat Type
- 16.10.8. Industry Protocol Security
- 16.10.9. End-users
- 16.11. Poland Industrial Cybersecurity Market
- 16.11.1. Country Segmental Analysis
- 16.11.2. Security Type
- 16.11.3. Component
- 16.11.4. Deployment Mode
- 16.11.5. Organization Size
- 16.11.6. Technology
- 16.11.7. Threat Type
- 16.11.8. Industry Protocol Security
- 16.11.9. End-users
- 16.12. Russia & CIS Industrial Cybersecurity Market
- 16.12.1. Country Segmental Analysis
- 16.12.2. Security Type
- 16.12.3. Component
- 16.12.4. Deployment Mode
- 16.12.5. Organization Size
- 16.12.6. Technology
- 16.12.7. Threat Type
- 16.12.8. Industry Protocol Security
- 16.12.9. End-users
- 16.13. Rest of Europe Industrial Cybersecurity Market
- 16.13.1. Country Segmental Analysis
- 16.13.2. Security Type
- 16.13.3. Component
- 16.13.4. Deployment Mode
- 16.13.5. Organization Size
- 16.13.6. Technology
- 16.13.7. Threat Type
- 16.13.8. Industry Protocol Security
- 16.13.9. End-users
- 17. Asia Pacific Industrial Cybersecurity Market Analysis
- 17.1. Key Segment Analysis
- 17.2. Regional Snapshot
- 17.3. Asia Pacific Industrial Cybersecurity Market Size Value (US$ Bn), Analysis, and Forecasts, 2021-2035
- 17.3.1. Security Type
- 17.3.2. Component
- 17.3.3. Deployment Mode
- 17.3.4. Organization Size
- 17.3.5. Technology
- 17.3.6. Threat Type
- 17.3.7. Industry Protocol Security
- 17.3.8. End-users
- 17.3.9. Country
- 17.3.9.1. China
- 17.3.9.2. India
- 17.3.9.3. Japan
- 17.3.9.4. South Korea
- 17.3.9.5. Australia and New Zealand
- 17.3.9.6. Indonesia
- 17.3.9.7. Malaysia
- 17.3.9.8. Thailand
- 17.3.9.9. Vietnam
- 17.3.9.10. Rest of Asia Pacific
- 17.4. China Industrial Cybersecurity Market
- 17.4.1. Country Segmental Analysis
- 17.4.2. Security Type
- 17.4.3. Component
- 17.4.4. Deployment Mode
- 17.4.5. Organization Size
- 17.4.6. Technology
- 17.4.7. Threat Type
- 17.4.8. Industry Protocol Security
- 17.4.9. End-users
- 17.5. India Industrial Cybersecurity Market
- 17.5.1. Country Segmental Analysis
- 17.5.2. Security Type
- 17.5.3. Component
- 17.5.4. Deployment Mode
- 17.5.5. Organization Size
- 17.5.6. Technology
- 17.5.7. Threat Type
- 17.5.8. Industry Protocol Security
- 17.5.9. End-users
- 17.6. Japan Industrial Cybersecurity Market
- 17.6.1. Country Segmental Analysis
- 17.6.2. Security Type
- 17.6.3. Component
- 17.6.4. Deployment Mode
- 17.6.5. Organization Size
- 17.6.6. Technology
- 17.6.7. Threat Type
- 17.6.8. Industry Protocol Security
- 17.6.9. End-users
- 17.7. South Korea Industrial Cybersecurity Market
- 17.7.1. Country Segmental Analysis
- 17.7.2. Security Type
- 17.7.3. Component
- 17.7.4. Deployment Mode
- 17.7.5. Organization Size
- 17.7.6. Technology
- 17.7.7. Threat Type
- 17.7.8. Industry Protocol Security
- 17.7.9. End-users
- 17.8. Australia and New Zealand Industrial Cybersecurity Market
- 17.8.1. Country Segmental Analysis
- 17.8.2. Security Type
- 17.8.3. Component
- 17.8.4. Deployment Mode
- 17.8.5. Organization Size
- 17.8.6. Technology
- 17.8.7. Threat Type
- 17.8.8. Industry Protocol Security
- 17.8.9. End-users
- 17.9. Indonesia Industrial Cybersecurity Market
- 17.9.1. Country Segmental Analysis
- 17.9.2. Security Type
- 17.9.3. Component
- 17.9.4. Deployment Mode
- 17.9.5. Organization Size
- 17.9.6. Technology
- 17.9.7. Threat Type
- 17.9.8. Industry Protocol Security
- 17.9.9. End-users
- 17.10. Malaysia Industrial Cybersecurity Market
- 17.10.1. Country Segmental Analysis
- 17.10.2. Security Type
- 17.10.3. Component
- 17.10.4. Deployment Mode
- 17.10.5. Organization Size
- 17.10.6. Technology
- 17.10.7. Threat Type
- 17.10.8. Industry Protocol Security
- 17.10.9. End-users
- 17.11. Thailand Industrial Cybersecurity Market
- 17.11.1. Country Segmental Analysis
- 17.11.2. Security Type
- 17.11.3. Component
- 17.11.4. Deployment Mode
- 17.11.5. Organization Size
- 17.11.6. Technology
- 17.11.7. Threat Type
- 17.11.8. Industry Protocol Security
- 17.11.9. End-users
- 17.12. Vietnam Industrial Cybersecurity Market
- 17.12.1. Country Segmental Analysis
- 17.12.2. Security Type
- 17.12.3. Component
- 17.12.4. Deployment Mode
- 17.12.5. Organization Size
- 17.12.6. Technology
- 17.12.7. Threat Type
- 17.12.8. Industry Protocol Security
- 17.12.9. End-users
- 17.13. Rest of Asia Pacific Industrial Cybersecurity Market
- 17.13.1. Country Segmental Analysis
- 17.13.2. Security Type
- 17.13.3. Component
- 17.13.4. Deployment Mode
- 17.13.5. Organization Size
- 17.13.6. Technology
- 17.13.7. Threat Type
- 17.13.8. Industry Protocol Security
- 17.13.9. End-users
- 18. Middle East Industrial Cybersecurity Market Analysis
- 18.1. Key Segment Analysis
- 18.2. Regional Snapshot
- 18.3. Middle East Industrial Cybersecurity Market Size Value (US$ Bn), Analysis, and Forecasts, 2021-2035
- 18.3.1. Security Type
- 18.3.2. Component
- 18.3.3. Deployment Mode
- 18.3.4. Organization Size
- 18.3.5. Technology
- 18.3.6. Threat Type
- 18.3.7. Industry Protocol Security
- 18.3.8. End-users
- 18.3.9. Country
- 18.3.9.1. Turkey
- 18.3.9.2. UAE
- 18.3.9.3. Saudi Arabia
- 18.3.9.4. Israel
- 18.3.9.5. Rest of Middle East
- 18.4. Turkey Industrial Cybersecurity Market
- 18.4.1. Country Segmental Analysis
- 18.4.2. Security Type
- 18.4.3. Component
- 18.4.4. Deployment Mode
- 18.4.5. Organization Size
- 18.4.6. Technology
- 18.4.7. Threat Type
- 18.4.8. Industry Protocol Security
- 18.4.9. End-users
- 18.5. UAE Industrial Cybersecurity Market
- 18.5.1. Country Segmental Analysis
- 18.5.2. Security Type
- 18.5.3. Component
- 18.5.4. Deployment Mode
- 18.5.5. Organization Size
- 18.5.6. Technology
- 18.5.7. Threat Type
- 18.5.8. Industry Protocol Security
- 18.5.9. End-users
- 18.6. Saudi Arabia Industrial Cybersecurity Market
- 18.6.1. Country Segmental Analysis
- 18.6.2. Security Type
- 18.6.3. Component
- 18.6.4. Deployment Mode
- 18.6.5. Organization Size
- 18.6.6. Technology
- 18.6.7. Threat Type
- 18.6.8. Industry Protocol Security
- 18.6.9. End-users
- 18.7. Israel Industrial Cybersecurity Market
- 18.7.1. Country Segmental Analysis
- 18.7.2. Security Type
- 18.7.3. Component
- 18.7.4. Deployment Mode
- 18.7.5. Organization Size
- 18.7.6. Technology
- 18.7.7. Threat Type
- 18.7.8. Industry Protocol Security
- 18.7.9. End-users
- 18.8. Rest of Middle East Industrial Cybersecurity Market
- 18.8.1. Country Segmental Analysis
- 18.8.2. Security Type
- 18.8.3. Component
- 18.8.4. Deployment Mode
- 18.8.5. Organization Size
- 18.8.6. Technology
- 18.8.7. Threat Type
- 18.8.8. Industry Protocol Security
- 18.8.9. End-users
- 19. Africa Industrial Cybersecurity Market Analysis
- 19.1. Key Segment Analysis
- 19.2. Regional Snapshot
- 19.3. Africa Industrial Cybersecurity Market Size Value (US$ Bn), Analysis, and Forecasts, 2021-2035
- 19.3.1. Security Type
- 19.3.2. Component
- 19.3.3. Deployment Mode
- 19.3.4. Organization Size
- 19.3.5. Technology
- 19.3.6. Threat Type
- 19.3.7. Industry Protocol Security
- 19.3.8. End-users
- 19.3.9. Country
- 19.3.9.1. South Africa
- 19.3.9.2. Egypt
- 19.3.9.3. Nigeria
- 19.3.9.4. Algeria
- 19.3.9.5. Rest of Africa
- 19.4. South Africa Industrial Cybersecurity Market
- 19.4.1. Country Segmental Analysis
- 19.4.2. Security Type
- 19.4.3. Component
- 19.4.4. Deployment Mode
- 19.4.5. Organization Size
- 19.4.6. Technology
- 19.4.7. Threat Type
- 19.4.8. Industry Protocol Security
- 19.4.9. End-users
- 19.5. Egypt Industrial Cybersecurity Market
- 19.5.1. Country Segmental Analysis
- 19.5.2. Security Type
- 19.5.3. Component
- 19.5.4. Deployment Mode
- 19.5.5. Organization Size
- 19.5.6. Technology
- 19.5.7. Threat Type
- 19.5.8. Industry Protocol Security
- 19.5.9. End-users
- 19.6. Nigeria Industrial Cybersecurity Market
- 19.6.1. Country Segmental Analysis
- 19.6.2. Security Type
- 19.6.3. Component
- 19.6.4. Deployment Mode
- 19.6.5. Organization Size
- 19.6.6. Technology
- 19.6.7. Threat Type
- 19.6.8. Industry Protocol Security
- 19.6.9. End-users
- 19.7. Algeria Industrial Cybersecurity Market
- 19.7.1. Country Segmental Analysis
- 19.7.2. Security Type
- 19.7.3. Component
- 19.7.4. Deployment Mode
- 19.7.5. Organization Size
- 19.7.6. Technology
- 19.7.7. Threat Type
- 19.7.8. Industry Protocol Security
- 19.7.9. End-users
- 19.8. Rest of Africa Industrial Cybersecurity Market
- 19.8.1. Country Segmental Analysis
- 19.8.2. Security Type
- 19.8.3. Component
- 19.8.4. Deployment Mode
- 19.8.5. Organization Size
- 19.8.6. Technology
- 19.8.7. Threat Type
- 19.8.8. Industry Protocol Security
- 19.8.9. End-users
- 20. South America Industrial Cybersecurity Market Analysis
- 20.1. Key Segment Analysis
- 20.2. Regional Snapshot
- 20.3. South America Industrial Cybersecurity Market Size Value (US$ Bn), Analysis, and Forecasts, 2021-2035
- 20.3.1. Security Type
- 20.3.2. Component
- 20.3.3. Deployment Mode
- 20.3.4. Organization Size
- 20.3.5. Technology
- 20.3.6. Threat Type
- 20.3.7. Industry Protocol Security
- 20.3.8. End-users
- 20.3.9. Country
- 20.3.9.1. Brazil
- 20.3.9.2. Argentina
- 20.3.9.3. Rest of South America
- 20.4. Brazil Industrial Cybersecurity Market
- 20.4.1. Country Segmental Analysis
- 20.4.2. Security Type
- 20.4.3. Component
- 20.4.4. Deployment Mode
- 20.4.5. Organization Size
- 20.4.6. Technology
- 20.4.7. Threat Type
- 20.4.8. Industry Protocol Security
- 20.4.9. End-users
- 20.5. Argentina Industrial Cybersecurity Market
- 20.5.1. Country Segmental Analysis
- 20.5.2. Security Type
- 20.5.3. Component
- 20.5.4. Deployment Mode
- 20.5.5. Organization Size
- 20.5.6. Technology
- 20.5.7. Threat Type
- 20.5.8. Industry Protocol Security
- 20.5.9. End-users
- 20.6. Rest of South America Industrial Cybersecurity Market
- 20.6.1. Country Segmental Analysis
- 20.6.2. Security Type
- 20.6.3. Component
- 20.6.4. Deployment Mode
- 20.6.5. Organization Size
- 20.6.6. Technology
- 20.6.7. Threat Type
- 20.6.8. Industry Protocol Security
- 20.6.9. End-users
- 21. Key Players/ Company Profile
- 21.1. ABB
- 21.1.1. Company Details/ Overview
- 21.1.2. Company Financials
- 21.1.3. Key Customers and Competitors
- 21.1.4. Business/ Industry Portfolio
- 21.1.5. Product Portfolio/ Specification Details
- 21.1.6. Pricing Data
- 21.1.7. Strategic Overview
- 21.1.8. Recent Developments
- 21.2. Check Point Software Technologies
- 21.3. Cisco Systems
- 21.4. Claroty
- 21.5. CrowdStrike
- 21.6. Dragos
- 21.7. FireEye (Trellix)
- 21.8. Fortified Health Security
- 21.9. Fortinet
- 21.10. Honeywell International
- 21.11. IBM Corporation
- 21.12. Kaspersky Lab
- 21.13. McAfee
- 21.14. Nozomi Networks
- 21.15. Palo Alto Networks
- 21.16. Rockwell Automation
- 21.17. Schneider Electric
- 21.18. Siemens
- 21.19. Symantec (Broadcom)
- 21.20. Trend Micro
- 21.21. Other Key Players
- 21.1. ABB
Note* - This is just tentative list of players. While providing the report, we will cover more number of players based on their revenue and share for each geography
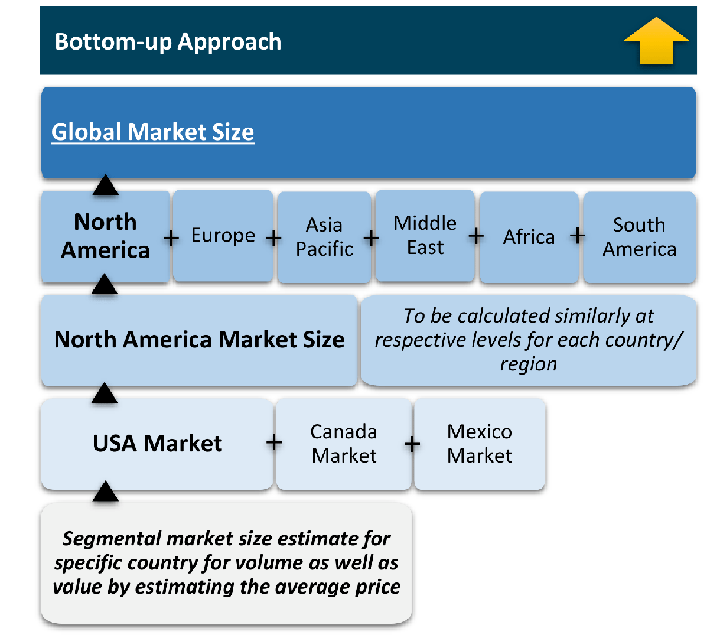
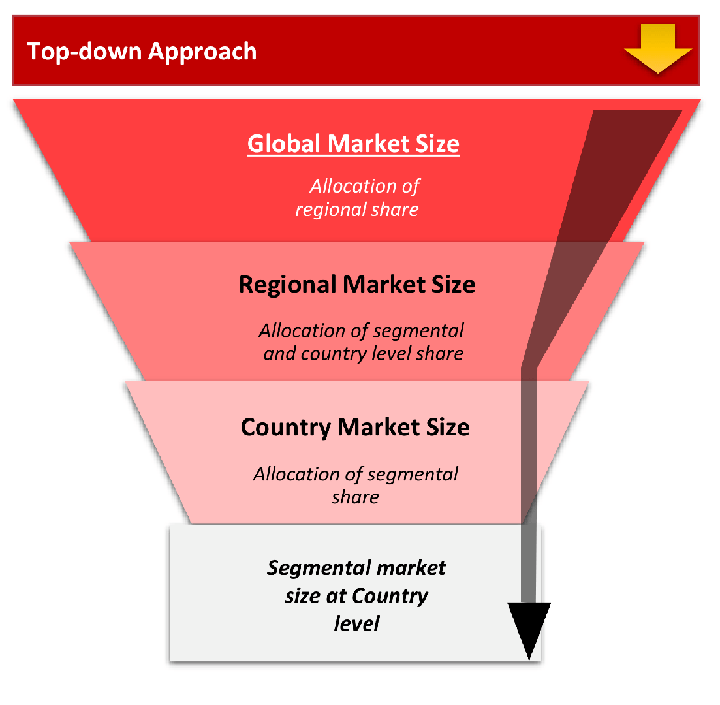
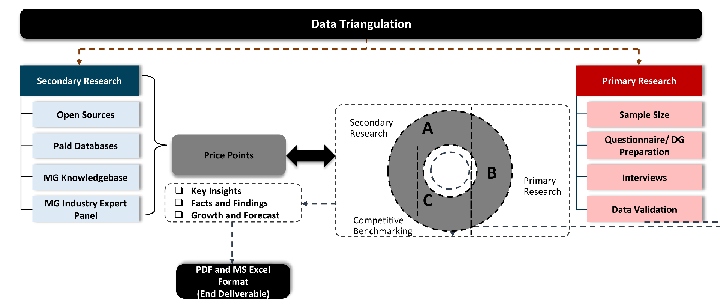
Research Design
Our research design integrates both demand-side and supply-side analysis through a balanced combination of primary and secondary research methodologies. By utilizing both bottom-up and top-down approaches alongside rigorous data triangulation methods, we deliver robust market intelligence that supports strategic decision-making.
MarketGenics' comprehensive research design framework ensures the delivery of accurate, reliable, and actionable market intelligence. Through the integration of multiple research approaches, rigorous validation processes, and expert analysis, we provide our clients with the insights needed to make informed strategic decisions and capitalize on market opportunities.
MarketGenics leverages a dedicated industry panel of experts and a comprehensive suite of paid databases to effectively collect, consolidate, and analyze market intelligence.
Our approach has consistently proven to be reliable and effective in generating accurate market insights, identifying key industry trends, and uncovering emerging business opportunities.
Through both primary and secondary research, we capture and analyze critical company-level data such as manufacturing footprints, including technical centers, R&D facilities, sales offices, and headquarters.
Our expert panel further enhances our ability to estimate market size for specific brands based on validated field-level intelligence.
Our data mining techniques incorporate both parametric and non-parametric methods, allowing for structured data collection, sorting, processing, and cleaning.
Demand projections are derived from large-scale data sets analyzed through proprietary algorithms, culminating in robust and reliable market sizing.
Research Approach
The bottom-up approach builds market estimates by starting with the smallest addressable market units and systematically aggregating them to create comprehensive market size projections.
This method begins with specific, granular data points and builds upward to create the complete market landscape.
Customer Analysis → Segmental Analysis → Geographical Analysis
The top-down approach starts with the broadest possible market data and systematically narrows it down through a series of filters and assumptions to arrive at specific market segments or opportunities.
This method begins with the big picture and works downward to increasingly specific market slices.
TAM → SAM → SOM
Research Methods
Desk / Secondary Research
While analysing the market, we extensively study secondary sources, directories, and databases to identify and collect information useful for this technical, market-oriented, and commercial report. Secondary sources that we utilize are not only the public sources, but it is a combination of Open Source, Associations, Paid Databases, MG Repository & Knowledgebase, and others.
- Company websites, annual reports, financial reports, broker reports, and investor presentations
- National government documents, statistical databases and reports
- News articles, press releases and web-casts specific to the companies operating in the market, Magazines, reports, and others
- We gather information from commercial data sources for deriving company specific data such as segmental revenue, share for geography, product revenue, and others
- Internal and external proprietary databases (industry-specific), relevant patent, and regulatory databases
- Governing Bodies, Government Organizations
- Relevant Authorities, Country-specific Associations for Industries
We also employ the model mapping approach to estimate the product level market data through the players' product portfolio
Primary Research
Primary research/ interviews is vital in analyzing the market. Most of the cases involves paid primary interviews. Primary sources include primary interviews through e-mail interactions, telephonic interviews, surveys as well as face-to-face interviews with the different stakeholders across the value chain including several industry experts.
| Type of Respondents | Number of Primaries |
|---|---|
| Tier 2/3 Suppliers | ~20 |
| Tier 1 Suppliers | ~25 |
| End-users | ~25 |
| Industry Expert/ Panel/ Consultant | ~30 |
| Total | ~100 |
MG Knowledgebase
• Repository of industry blog, newsletter and case studies
• Online platform covering detailed market reports, and company profiles
Forecasting Factors and Models
Forecasting Factors
- Historical Trends – Past market patterns, cycles, and major events that shaped how markets behave over time. Understanding past trends helps predict future behavior.
- Industry Factors – Specific characteristics of the industry like structure, regulations, and innovation cycles that affect market dynamics.
- Macroeconomic Factors – Economic conditions like GDP growth, inflation, and employment rates that affect how much money people have to spend.
- Demographic Factors – Population characteristics like age, income, and location that determine who can buy your product.
- Technology Factors – How quickly people adopt new technology and how much technology infrastructure exists.
- Regulatory Factors – Government rules, laws, and policies that can help or restrict market growth.
- Competitive Factors – Analyzing competition structure such as degree of competition and bargaining power of buyers and suppliers.
Forecasting Models / Techniques
Multiple Regression Analysis
- Identify and quantify factors that drive market changes
- Statistical modeling to establish relationships between market drivers and outcomes
Time Series Analysis – Seasonal Patterns
- Understand regular cyclical patterns in market demand
- Advanced statistical techniques to separate trend, seasonal, and irregular components
Time Series Analysis – Trend Analysis
- Identify underlying market growth patterns and momentum
- Statistical analysis of historical data to project future trends
Expert Opinion – Expert Interviews
- Gather deep industry insights and contextual understanding
- In-depth interviews with key industry stakeholders
Multi-Scenario Development
- Prepare for uncertainty by modeling different possible futures
- Creating optimistic, pessimistic, and most likely scenarios
Time Series Analysis – Moving Averages
- Sophisticated forecasting for complex time series data
- Auto-regressive integrated moving average models with seasonal components
Econometric Models
- Apply economic theory to market forecasting
- Sophisticated economic models that account for market interactions
Expert Opinion – Delphi Method
- Harness collective wisdom of industry experts
- Structured, multi-round expert consultation process
Monte Carlo Simulation
- Quantify uncertainty and probability distributions
- Thousands of simulations with varying input parameters
Research Analysis
Our research framework is built upon the fundamental principle of validating market intelligence from both demand and supply perspectives. This dual-sided approach ensures comprehensive market understanding and reduces the risk of single-source bias.
Demand-Side Analysis: We understand end-user/application behavior, preferences, and market needs along with the penetration of the product for specific application.
Supply-Side Analysis: We estimate overall market revenue, analyze the segmental share along with industry capacity, competitive landscape, and market structure.
Validation & Evaluation
Data triangulation is a validation technique that uses multiple methods, sources, or perspectives to examine the same research question, thereby increasing the credibility and reliability of research findings. In market research, triangulation serves as a quality assurance mechanism that helps identify and minimize bias, validate assumptions, and ensure accuracy in market estimates.
- Data Source Triangulation – Using multiple data sources to examine the same phenomenon
- Methodological Triangulation – Using multiple research methods to study the same research question
- Investigator Triangulation – Using multiple researchers or analysts to examine the same data
- Theoretical Triangulation – Using multiple theoretical perspectives to interpret the same data
Custom Market Research Services
We will customise the research for you, in case the report listed above does not meet your requirements.
Get 10% Free Customisation