Privacy-Enhancing Computation (PEC) Technologies Market Size, Share & Trends Analysis Report by Technology Type (Homomorphic Encryption (FHE, SHE, PHE), Secure Multiparty Computation (MPC), Differential Privacy, Federated Learning, Trusted Execution Environments (TEE), Zero-Knowledge Proofs (ZKP), Data Anonymization & Masking, Synthetic Data Generation, Secure Query & Retrieval Systems, Secure Data Collaboration Platforms and Others), Deployment Mode, Component, Compute Architecture, Data Type, Organization Size, Application, Industry Vertical and Geography (North America, Europe, Asia Pacific, Middle East, Africa, and South America) – Global Industry Data, Trends, and Forecasts, 2026–2035
|
Market Structure & Evolution |
|
|
Segmental Data Insights |
|
|
Demand Trends |
|
|
Competitive Landscape |
|
|
Strategic Development |
|
|
Future Outlook & Opportunities |
|
Privacy-Enhancing Computation (PEC) Technologies Market Size, Share, and Growth
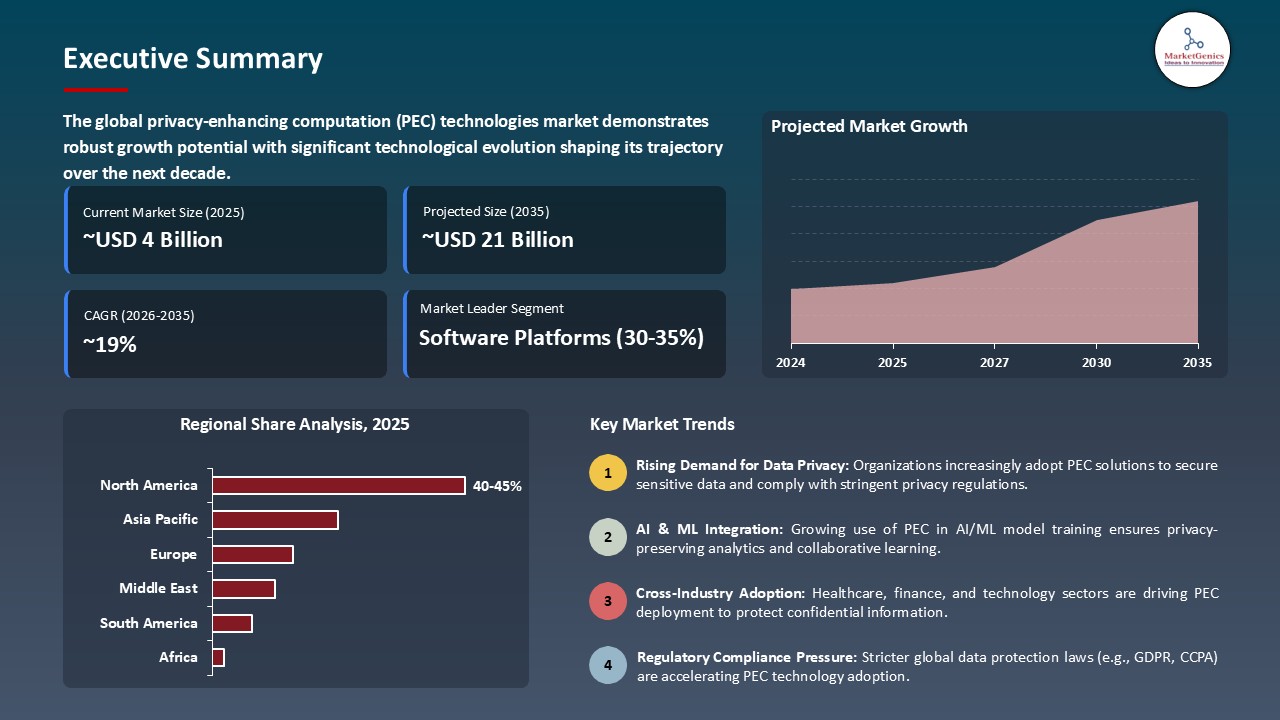
The global privacy-enhancing computation (PEC) technologies market is experiencing robust growth, with its estimated value of USD 3.6 billion in the year 2025 and USD 20.9 billion by the period 2035, registering a CAGR of 19.2% during the forecast period.
“Data must stay protected - even while it’s being used,” as per Flavio Bergamaschi, Chief Technology Officer of Private AI and Analytics at Intel. In his opinion, privacy-enhancing computation (PEC) instruments such as fully homomorphic encryption are indispensable as they allow companies to perform analytics on encrypted data without exposing it, thus facilitating collaboration and AI,”
The privacy-enhancing computation (PEC) technologies market is going very fast all over the world, and this change is mainly caused by the demand for a secure way of data collaboration and confidential computing. One such example is IBM Research, which, through its HElayers SDK, is making Fully Homomorphic Encryption (FHE) more feasible so that organizations can run AI workloads on data that is encrypted at all times without the need to expose the raw inputs.
For instance, in October 2025, Duality Technologies joined forces with Oracle to debut its platform for secure data collaboration on Oracle Cloud Infrastructure. The platform features homomorphic encryption, secure multi-party computation (MPC), and federated learning as enabling technologies for encrypted queries and confidential analysis at scale.
The regulatory pressures in the form of strict data privacy laws and AI regulations are the reasons for this growth as well, and hence, they are pushing enterprises to adopt privacy-enhancing computation instruments not only for the purpose of compliance but also for gaining competitive intelligence. Besides that, the advancement of technology (e.g., FHE and confidential computing) is making such solutions more and more viable in the real world.
The adjacent market opportunities for privacy-enhancing computation are confidential cloud computing, privacy-preserving AI platforms, encrypted data marketplaces, and secure analytics ecosystems. While, privacy-enhancing computation providers delve into these, they not only secure data protection but also create different revenue streams that extend their business models in the broader cybersecurity and data-privacy landscape.
Privacy Enhancing Computation Technologies Market Dynamics and Trends
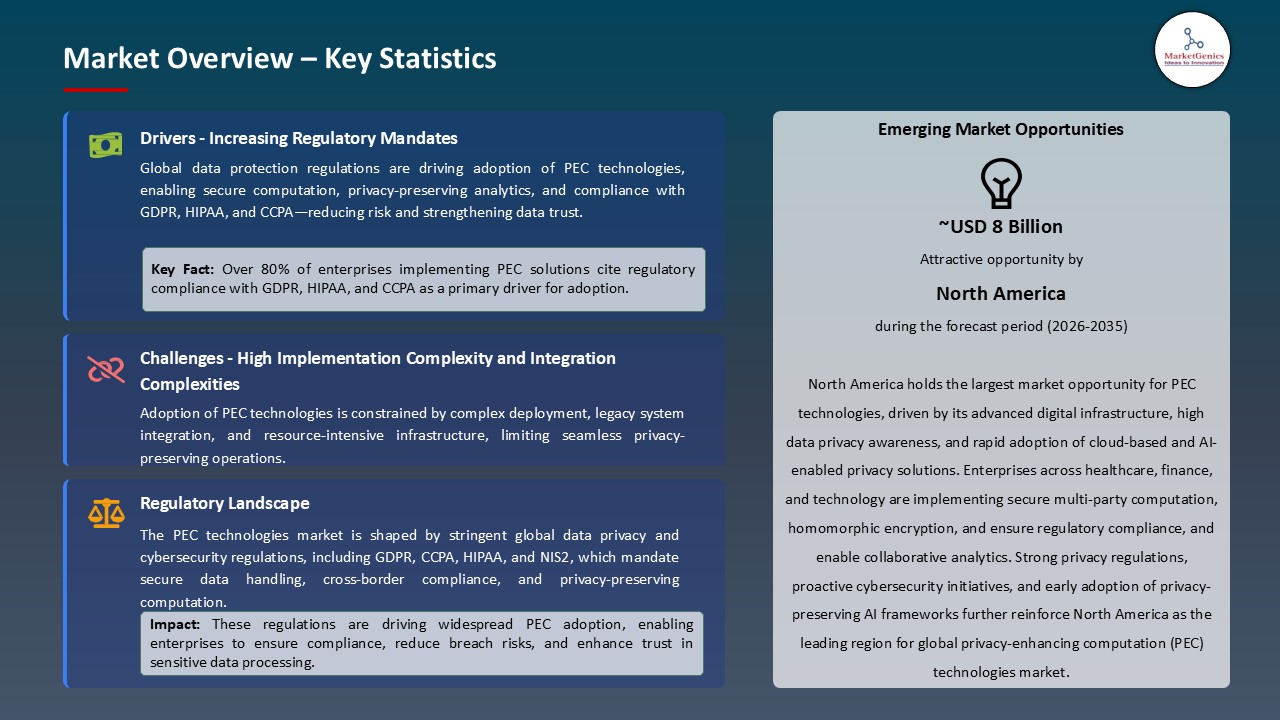
Driver: Increasing Regulatory Mandates Driving Adoption of PEC Technologies
- Worldwide rules concerning data privacy and security, like GDPR in Europe, the California Consumer Privacy Act (CCPA), and the coming EU AI Act, are the reasons why companies are implementing privacy-enhancing computation (PEC) technologies to not only be in line with these regulations but also to allow secure analytics on confidential data.
- Recent regulations in the Asia-Pacific and North America regions, such as the updates to Singapore’s Personal Data Protection Act (PDPA) and the U.S. Executive Order on AI, highlight the requirement for privacy-preserving analytics, thus speeding up PEC use in the finance, healthcare, and government sectors. In October 2025, a collaboration between Duality Technologies and Oracle led to the creation of secure collaborative AI platforms that support homomorphic encryption and multi-party computation, thus serving as an example of the worldwide trend of integrating privacy-first computation into workflows of enterprises.
- The growing use of AI in vital business operations, together with the increase of cyber threats, has turned privacy-enhancing computation technologies into a strategic tool that enterprises must have if they want to protect sensitive data and at the same time keep their operations running efficiently.
Restraint: High Implementation Complexity and Integration Challenges Limiting Privacy-Enhancing Computation (PEC) Technologies Awareness
- One of the major challenges in the widespread use of privacy-enhancing computation solutions is the technical difficulty of integrating encrypted computation methods such as homomorphic encryption, secure multi-party computation (MPC), and federated learning into already existing IT and data pipelines. Enterprises having legacy data systems or siloed infrastructure are blocked by significant barriers that include the costs of API development, encrypted data storage, and secure key management.
- In order to keep the system efficient while handling encrypted data is something that requires specialized knowledge and computing power, thus making the implementation of privacy-enhancing computation a difficult task for SMEs and public-sector organizations that do not have a considerable amount of money to invest.
- Besides that, these kinds of organizations are frequently struggling with scaling their PEC solutions in multi-cloud or hybrid environments, which in turn slows down a large-scale adoption even though there are clear incentives from the regulatory side.
Opportunity: Expansion in Cloud-Based PEC Services and Industry-Specific Use Cases
- The rise of cloud computing and the increased use of AI are leading to new possibilities for privacy-enhancing computation -as-a-service business models, where cloud providers offer confidential computing platforms that clients can use to run secure workloads. The spread of privacy-enhancing computation usage is happening in finance for fraud detection, in healthcare for collaborative research on patient data, and in government for confidential inter-agency data sharing.
- On the contrary, companies like IBM, Duality Technologies, and Enveil are providing the means for secure analytics on encrypted datasets, thus enabling organizations to gain insights without revealing sensitive information - thereby facilitating enterprise adoption worldwide.
- Furthermore, the growing desire for cross-organizational data collaborations, e.g., consortium-based research and industry-wide benchmarking, is resulting in expanding privacy-enhancing computation solutions market.
Key Trend: Integration of AI, Federated Learning, and Confidential Computing making Shift towards Privacy-Enhancing Computation (PEC) Technologies Evolution
- New generation PEC platforms are using AI-driven analytics together with federated learning, which allows models to be trained on several encrypted datasets without the need to change the data. As part of efforts to enhance data security, confidential computing technologies like Trusted Execution Environment (TEEs) are being implemented in both cloud and on-premises facilities.
- The shift towards privacy-by-design along with verifiable computation and secure analytics frameworks is giving organizations the freedom to derive valuable insights from data while still adhering to regulations, thus a major change in trust for collaboration with sensitive data across industries.
- Additionally, the development of zero-knowledge proofs (ZKPs) and cryptographically verifiable computations is lifting the bar for transparency and recording-keeping in data sharing, hence sectors with great stakes such as healthcare, finance, and defense are leading the way in the implementation of the same.
Privacy Enhancing Computation Technologies Market Analysis and Segmental Data
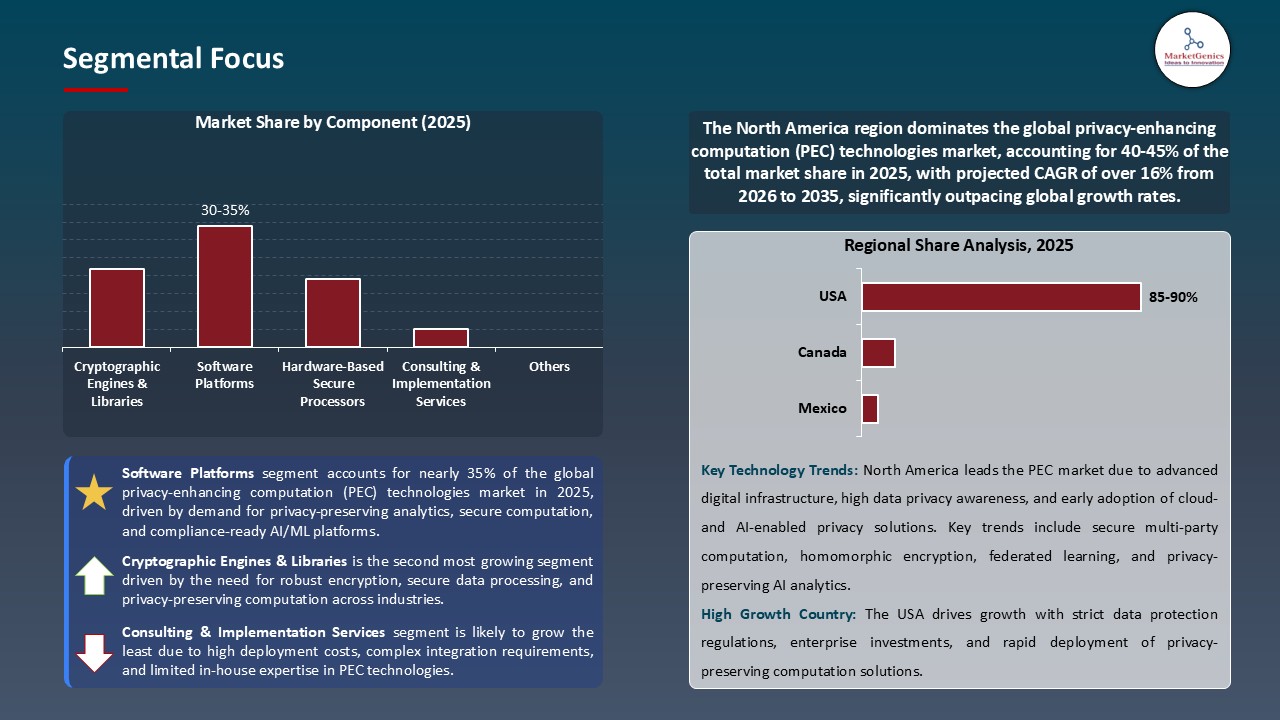
“Software Platforms Dominates Global Privacy-Enhancing Computation (PEC) Technologies Market amid Rising Demand for Secure Data Collaboration and Regulatory Compliance"
- Software platforms lead the global privacy-enhancing computation (PEC) market by value as they are the primary choice to address the rising need for secure data collaboration and regulatory compliance. They offer scalable, enterprise-grade tools to perform computations on encrypted data without exposing the raw inputs.
- As an illustration, in October 2025, Duality Technologies launched its secure data collaboration platform - which supports homomorphic encryption (HE), multiparty computation (MPC), and federated learning - on Oracle Cloud Infrastructure (OCI). These installations empower the execution of sensitive analytics in tightly secured environments like government and defense, at the same time, complying with strict regulatory standards.
- On the contrary, inventions for the future, such as Hermes, a high-performance FHE-native vector database, are accelerating the transition of privacy-enhancing computation from a theoretical concept to a real-world solution. Software platforms have also enabled the integration of AI-driven analytics, federated learning, and confidential computing frameworks, thereby companies can run privacy-preserving machine learning models and data sharing projects across various entities.
- Owing to more stringent regulatory requirements such as GDPR, CCPA, and the forthcoming EU AI Act, privacy-enhancing computation software platforms have become indispensable in the finance, healthcare, and cloud service sectors that need to ensure compliance and operational efficiency.
“North America Leads Privacy-Enhancing Computation (PEC) Technologies Market with Advanced Data Privacy Adoption and Strong Regulatory Compliance"
- Driven by its sophisticated digital infrastructure, the presence of tech giants, and a well-established regulatory environment, North America is at the forefront of the global privacy‑enhancing computation (PEC) technologies market. Besides the U.S., Canada is home to leading cloud providers, cryptography researchers, and startups that fuel innovation in homomorphic encryption, secure multi‑party computation, and confidential computing.
- Tight data privacy laws such as the California Consumer Privacy Act (CCPA) and sector-specific standards like HIPAA force organizations to take privacy‑enhancing computation measures to protect sensitive data and comply with regulations. North American businesses, especially those in the finance, healthcare, and government sectors, are pioneering the use of privacy-preserving analytics, thus employing PEC to collaboratively and securely execute AI.
- Notably, IBM has moved its Hyper Protect confidential-computing offering to Red Hat’s container ecosystem, thus enabling TEEs (Trusted Execution Environments) for hybrid cloud workloads.
- Additionally, Fortanix collaborated with Carahsoft in November 2024 to provide U.S. federal agencies with its confidential-computing and post-quantum cryptography solutions - a perfect example of North America's demand driven by regulations. Driven by continually increasing cyber threats and investments in AI-enabled SOCs and other cloud-native controls, North America continues to set the global standard for zero trust maturity, regulatory coordination, and enterprise security modernization.
Privacy-Enhancing-Computation-Technologies-Market Ecosystem
The privacy-enhancing computation market is progressively getting highly consolidated with the number of players, with IBM, Microsoft, Google Cloud, Intel, Duality Technologies, Fortanix, Enveil, and Inpher as the main contributors that are leading this consolidation through their sophisticated confidential computing platforms, trusted enclave, secure multi-party computation (MPC), and fully homomorphic encryption (FHE) technologies. These companies are investing in niche, high-value PEC features-like IBM’s HElayers SDK for practical FHE, Microsoft Azure’s Confidential VMs, Google’s Assured Workloads, and Duality’s secure data collaboration tools-thereby powering the next wave of innovation and making scalable privacy-preserving analytics possible for regulated industries.
Government agencies, federal distributors, and research institutions are likewise driving the momentum of PEC innovation. For instance, Fortanix extended its confidential computing and post-quantum cryptography offering into U.S. federal deployment channels in November 2024, thus facilitating the public-sector adoption of next-generation privacy-preserving technologies.
Besides that, vendors are intensifying the emphasis on career and personality development with the help of MPC, FHE, federated learning, encrypted databases, and TEEs through integration into a single platform that offers enhanced security, better operational efficiency, and eases regulatory compliance.
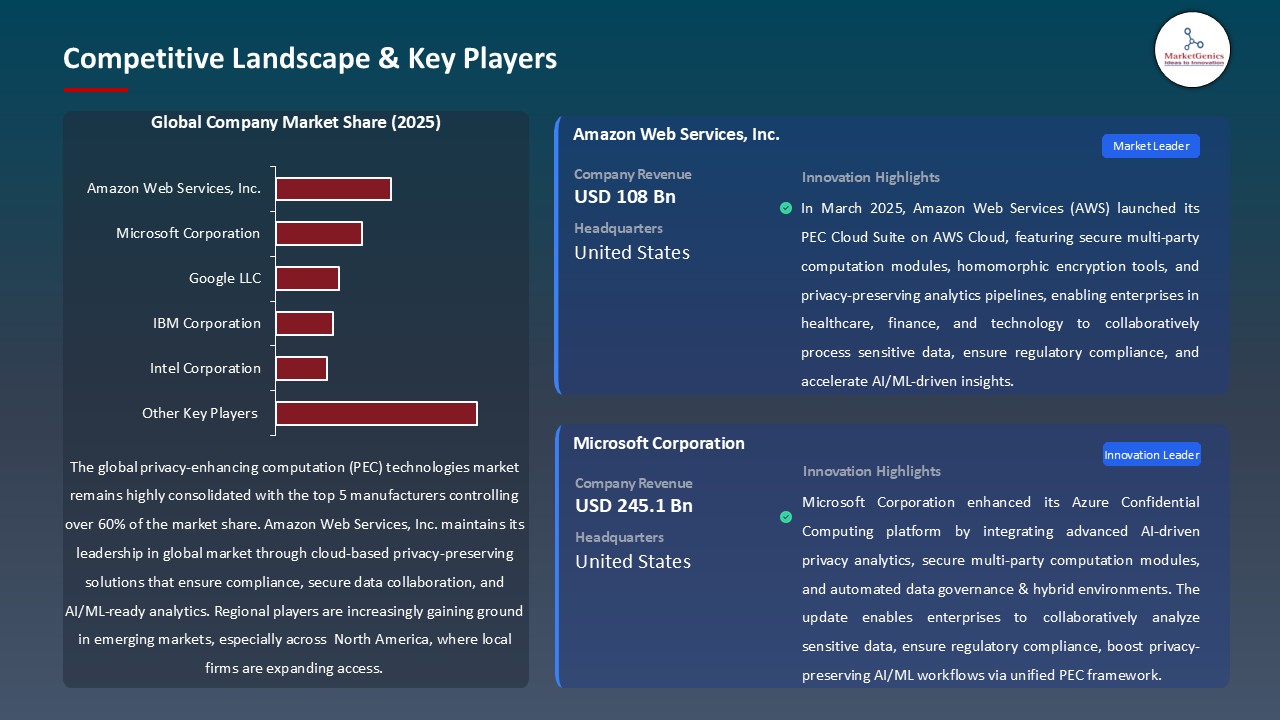
Recent Development and Strategic Overview:
- In March 2024, Google DeepMind made a significant change to its open-source Private Join and Compute framework by adding the capability for organizations to use secure multi-party computation (MPC) to perform encrypted data matching without revealing the underlying datasets. The change made cross-institution analytics more efficient in healthcare and finance. It also facilitated privacy-preserving data collaboration and lowered the risk of compliance with GDPR and HIPAA.
- In May 2024, Intel broadened its Confidential Computing range of offerings with the launch of Intel® Trust Domain Extensions (TDX) that is available across major cloud providers. It allows sensitive workloads, such as machine learning models and encrypted data processing, to be executed inside hardware-based trusted execution environments (TEEs). With this release, the enterprise customers were enabled to carry out the valuable analytics on the data that had been protected while at the same time maintain the verifiable isolation at the infrastructure layer. This is in line with the growing use of privacy-enhancing computation in the regulated sectors.
Report Scope
|
Attribute |
Detail |
|
Market Size in 2025 |
USD 3.6 Bn |
|
Market Forecast Value in 2035 |
USD 20.9 Bn |
|
Growth Rate (CAGR) |
19.2% |
|
Forecast Period |
2026 – 2035 |
|
Historical Data Available for |
2021 – 2024 |
|
Market Size Units |
USD Bn for Value |
|
Report Format |
Electronic (PDF) + Excel |
|
Regions and Countries Covered |
|||||
|
North America |
Europe |
Asia Pacific |
Middle East |
Africa |
South America |
|
|
|
|
|
|
|
Companies Covered |
|||||
|
|
|
|
|
|
Privacy-Enhancing-Computation-(PEC)-Technologies-Market Segmentation and Highlights
|
Segment |
Sub-segment |
|
Privacy-Enhancing Computation (PEC) Technologies Market, By Technology Type |
|
|
Privacy-Enhancing Computation (PEC) Technologies Market, By Deployment Mode |
|
|
Privacy-Enhancing Computation (PEC) Technologies Market, By Component |
|
|
Privacy-Enhancing Computation (PEC) Technologies Market, By Compute Architecture |
|
|
Privacy-Enhancing Computation (PEC) Technologies Market, By Data Type |
|
|
Privacy-Enhancing Computation (PEC) Technologies Market, By Organization Size |
|
|
Privacy-Enhancing Computation (PEC) Technologies Market, By Application |
|
|
Privacy-Enhancing Computation (PEC) Technologies Market, By Industry Vertical |
|
Frequently Asked Questions
Table of Contents
- 1. Research Methodology and Assumptions
- 1.1. Definitions
- 1.2. Research Design and Approach
- 1.3. Data Collection Methods
- 1.4. Base Estimates and Calculations
- 1.5. Forecasting Models
- 1.5.1. Key Forecast Factors & Impact Analysis
- 1.6. Secondary Research
- 1.6.1. Open Sources
- 1.6.2. Paid Databases
- 1.6.3. Associations
- 1.7. Primary Research
- 1.7.1. Primary Sources
- 1.7.2. Primary Interviews with Stakeholders across Ecosystem
- 2. Executive Summary
- 2.1. Global Privacy-Enhancing Computation (PEC) Technologies Market Outlook
- 2.1.1. Privacy-Enhancing Computation (PEC) Technologies Market Size (Value - US$ Bn), and Forecasts, 2021-2035
- 2.1.2. Compounded Annual Growth Rate Analysis
- 2.1.3. Growth Opportunity Analysis
- 2.1.4. Segmental Share Analysis
- 2.1.5. Geographical Share Analysis
- 2.2. Market Analysis and Facts
- 2.3. Supply-Demand Analysis
- 2.4. Competitive Benchmarking
- 2.5. Go-to- Market Strategy
- 2.5.1. Customer/ End-use Industry Assessment
- 2.5.2. Growth Opportunity Data, 2026-2035
- 2.5.2.1. Regional Data
- 2.5.2.2. Country Data
- 2.5.2.3. Segmental Data
- 2.5.3. Identification of Potential Market Spaces
- 2.5.4. GAP Analysis
- 2.5.5. Potential Attractive Price Points
- 2.5.6. Prevailing Market Risks & Challenges
- 2.5.7. Preferred Sales & Marketing Strategies
- 2.5.8. Key Recommendations and Analysis
- 2.5.9. A Way Forward
- 2.1. Global Privacy-Enhancing Computation (PEC) Technologies Market Outlook
- 3. Industry Data and Premium Insights
- 3.1. Global Information Technology & Media Ecosystem Overview, 2025
- 3.1.1. Information Technology & Media Industry Analysis
- 3.1.2. Key Trends for Information Technology & Media Industry
- 3.1.3. Regional Distribution for Information Technology & Media Industry
- 3.2. Supplier Customer Data
- 3.3. Technology Roadmap and Developments
- 3.1. Global Information Technology & Media Ecosystem Overview, 2025
- 4. Market Overview
- 4.1. Market Dynamics
- 4.1.1. Drivers
- 4.1.1.1. Rising need for secure, privacy-preserving computation across enterprises
- 4.1.1.2. Growing adoption of AI- and analytics-driven privacy-preserving solutions
- 4.1.1.3. Increasing regulatory requirements like GDPR, HIPAA, and CCPA
- 4.1.2. Restraints
- 4.1.2.1. High deployment and operational costs of PEC platforms
- 4.1.2.2. Integration challenges with legacy systems and diverse IT environments
- 4.1.1. Drivers
- 4.2. Key Trend Analysis
- 4.3. Regulatory Framework
- 4.3.1. Key Regulations, Norms, and Subsidies, by Key Countries
- 4.3.2. Tariffs and Standards
- 4.3.3. Impact Analysis of Regulations on the Market
- 4.4. Value Chain Analysis
- 4.4.1. Data Anonymization and Encryption Providers
- 4.4.2. System Integrators/ Technology Providers
- 4.4.3. PEC Technologies Providers
- 4.4.4. End Users
- 4.5. Cost Structure Analysis
- 4.5.1. Parameter’s Share for Cost Associated
- 4.5.2. COGP vs COGS
- 4.5.3. Profit Margin Analysis
- 4.6. Pricing Analysis
- 4.6.1. Regional Pricing Analysis
- 4.6.2. Segmental Pricing Trends
- 4.6.3. Factors Influencing Pricing
- 4.7. Porter’s Five Forces Analysis
- 4.8. PESTEL Analysis
- 4.9. Global Privacy-Enhancing Computation (PEC) Technologies Market Demand
- 4.9.1. Historical Market Size –Value (US$ Bn), 2020-2024
- 4.9.2. Current and Future Market Size –Value (US$ Bn), 2026–2035
- 4.9.2.1. Y-o-Y Growth Trends
- 4.9.2.2. Absolute $ Opportunity Assessment
- 4.1. Market Dynamics
- 5. Competition Landscape
- 5.1. Competition structure
- 5.1.1. Fragmented v/s consolidated
- 5.2. Company Share Analysis, 2025
- 5.2.1. Global Company Market Share
- 5.2.2. By Region
- 5.2.2.1. North America
- 5.2.2.2. Europe
- 5.2.2.3. Asia Pacific
- 5.2.2.4. Middle East
- 5.2.2.5. Africa
- 5.2.2.6. South America
- 5.3. Product Comparison Matrix
- 5.3.1. Specifications
- 5.3.2. Market Positioning
- 5.3.3. Pricing
- 5.1. Competition structure
- 6. Global Privacy-Enhancing Computation (PEC) Technologies Market Analysis, by Technology Type
- 6.1. Key Segment Analysis
- 6.2. Privacy-Enhancing Computation (PEC) Technologies Market Size (Value - US$ Bn), Analysis, and Forecasts, by Technology Type, 2021-2035
- 6.2.1. Homomorphic Encryption (FHE, SHE, PHE)
- 6.2.2. Secure Multiparty Computation (MPC)
- 6.2.3. Differential Privacy
- 6.2.4. Federated Learning
- 6.2.5. Trusted Execution Environments (TEE)
- 6.2.6. Zero-Knowledge Proofs (ZKP)
- 6.2.7. Data Anonymization & Masking
- 6.2.8. Synthetic Data Generation
- 6.2.9. Secure Query & Retrieval Systems
- 6.2.10. Secure Data Collaboration Platforms
- 6.2.11. Others
- 7. Global Privacy-Enhancing Computation (PEC) Technologies Market Analysis, by Deployment Mode
- 7.1. Key Segment Analysis
- 7.2. Privacy-Enhancing Computation (PEC) Technologies Market Size (Value - US$ Bn), Analysis, and Forecasts, by Deployment Mode, 2021-2035
- 7.2.1. Cloud-Based
- 7.2.2. On-Premises
- 7.2.3. Hybrid
- 8. Global Privacy-Enhancing Computation (PEC) Technologies Market Analysis, by Component
- 8.1. Key Segment Analysis
- 8.2. Privacy-Enhancing Computation (PEC) Technologies Market Size (Value - US$ Bn), Analysis, and Forecasts, by Component, 2021-2035
- 8.2.1. Software Platforms
- 8.2.2. Cryptographic Engines & Libraries
- 8.2.3. Hardware-Based Secure Processors
- 8.2.4. Cloud Services
- 8.2.5. APIs & SDKs
- 8.2.6. Integration Middleware
- 8.2.7. Managed Privacy Services
- 8.2.8. Consulting & Implementation Services
- 8.2.9. Others
- 9. Global Privacy-Enhancing Computation (PEC) Technologies Market Analysis, by Compute Architecture
- 9.1. Key Segment Analysis
- 9.2. Privacy-Enhancing Computation (PEC) Technologies Market Size (Value - US$ Bn), Analysis, and Forecasts, by Compute Architecture, 2021-2035
- 9.2.1. CPU-Based Privacy Compute
- 9.2.2. GPU/Accelerator-Based Encryption Compute
- 9.2.3. Hardware-Embedded TEE Compute
- 9.2.4. Distributed/Federated Compute Nodes
- 9.2.5. Blockchain / Decentralized Compute
- 9.2.6. Others
- 10. Global Privacy-Enhancing Computation (PEC) Technologies Market Analysis, by Data Type
- 10.1. Key Segment Analysis
- 10.2. Privacy-Enhancing Computation (PEC) Technologies Market Size (Value - US$ Bn), Analysis, and Forecasts, by Data Type, 2021-2035
- 10.2.1. Structured Data
- 10.2.2. Unstructured Data
- 10.2.3. Semi-structured Data
- 10.2.4. Identity & Behavioral Data
- 10.2.5. Proprietary Enterprise Data
- 10.2.6. Others
- 11. Global Privacy-Enhancing Computation (PEC) Technologies Market Analysis, by Organization Size
- 11.1. Key Segment Analysis
- 11.2. Privacy-Enhancing Computation (PEC) Technologies Market Size (Value - US$ Bn), Analysis, and Forecasts, by Organization Size, 2021-2035
- 11.2.1. Large enterprises
- 11.2.2. Small & Medium-sized Enterprises (SMEs)
- 11.2.3. Individual users / consumers (verification apps)
- 12. Global Privacy-Enhancing Computation (PEC) Technologies Market Analysis, by Application
- 12.1. Key Segment Analysis
- 12.2. Privacy-Enhancing Computation (PEC) Technologies Market Size (Value - US$ Bn), Analysis, and Forecasts, by Application, 2021-2035
- 12.2.1. Secure Analytics & Data Processing
- 12.2.2. Privacy-Preserving AI & ML
- 12.2.3. Secure Data Sharing & Collaboration
- 12.2.4. Data Monetization with Privacy
- 12.2.5. Fraud Detection & Risk Modeling
- 12.2.6. Customer Identity Protection
- 12.2.7. Medical Data Sharing & Research
- 12.2.8. Federated Model Training
- 12.2.9. Cross-border Data Processing
- 12.2.10. Others
- 13. Global Privacy-Enhancing Computation (PEC) Technologies Market Analysis, by Industry Vertical
- 13.1. Key Segment Analysis
- 13.2. Privacy-Enhancing Computation (PEC) Technologies Market Size (Value - US$ Bn), Analysis, and Forecasts, by Industry Vertical, 2021-2035
- 13.2.1. Banking, Financial Services & Insurance (BFSI)
- 13.2.2. Healthcare & Life Sciences
- 13.2.3. Government & Defense
- 13.2.4. Retail & eCommerce
- 13.2.5. IT & Telecommunications
- 13.2.6. Energy & Utilities
- 13.2.7. Manufacturing
- 13.2.8. Transportation & Logistics
- 13.2.9. Media & Advertising
- 13.2.10. Education & Research
- 13.2.11. Others
- 14. Global Privacy-Enhancing Computation (PEC) Technologies Market Analysis and Forecasts, by Region
- 14.1. Key Findings
- 14.2. Privacy-Enhancing Computation (PEC) Technologies Market Size (Value - US$ Bn), Analysis, and Forecasts, by Region, 2021-2035
- 14.2.1. North America
- 14.2.2. Europe
- 14.2.3. Asia Pacific
- 14.2.4. Middle East
- 14.2.5. Africa
- 14.2.6. South America
- 15. North America Privacy-Enhancing Computation (PEC) Technologies Market Analysis
- 15.1. Key Segment Analysis
- 15.2. Regional Snapshot
- 15.3. North America Privacy-Enhancing Computation (PEC) Technologies Market Size Value - US$ Bn), Analysis, and Forecasts, 2021-2035
- 15.3.1. Technology Type
- 15.3.2. Deployment Mode
- 15.3.3. Component
- 15.3.4. Compute Architecture
- 15.3.5. Data Type
- 15.3.6. Organization Size
- 15.3.7. Application
- 15.3.8. Industry Vertical
- 15.3.9. Country
- 15.3.9.1. USA
- 15.3.9.2. Canada
- 15.3.9.3. Mexico
- 15.4. USA Privacy-Enhancing Computation (PEC) Technologies Market
- 15.4.1. Country Segmental Analysis
- 15.4.2. Technology Type
- 15.4.3. Deployment Mode
- 15.4.4. Component
- 15.4.5. Compute Architecture
- 15.4.6. Data Type
- 15.4.7. Organization Size
- 15.4.8. Application
- 15.4.9. Industry Vertical
- 15.5. Canada Privacy-Enhancing Computation (PEC) Technologies Market
- 15.5.1. Country Segmental Analysis
- 15.5.2. Technology Type
- 15.5.3. Deployment Mode
- 15.5.4. Component
- 15.5.5. Compute Architecture
- 15.5.6. Data Type
- 15.5.7. Organization Size
- 15.5.8. Application
- 15.5.9. Industry Vertical
- 15.6. Mexico Privacy-Enhancing Computation (PEC) Technologies Market
- 15.6.1. Country Segmental Analysis
- 15.6.2. Technology Type
- 15.6.3. Deployment Mode
- 15.6.4. Component
- 15.6.5. Compute Architecture
- 15.6.6. Data Type
- 15.6.7. Organization Size
- 15.6.8. Application
- 15.6.9. Industry Vertical
- 16. Europe Privacy-Enhancing Computation (PEC) Technologies Market Analysis
- 16.1. Key Segment Analysis
- 16.2. Regional Snapshot
- 16.3. Europe Privacy-Enhancing Computation (PEC) Technologies Market Size (Value - US$ Bn), Analysis, and Forecasts, 2021-2035
- 16.3.1. Technology Type
- 16.3.2. Deployment Mode
- 16.3.3. Component
- 16.3.4. Compute Architecture
- 16.3.5. Data Type
- 16.3.6. Organization Size
- 16.3.7. Application
- 16.3.8. Industry Vertical
- 16.3.9. Country
- 16.3.9.1. Germany
- 16.3.9.2. United Kingdom
- 16.3.9.3. France
- 16.3.9.4. Italy
- 16.3.9.5. Spain
- 16.3.9.6. Netherlands
- 16.3.9.7. Nordic Countries
- 16.3.9.8. Poland
- 16.3.9.9. Russia & CIS
- 16.3.9.10. Rest of Europe
- 16.4. Germany Privacy-Enhancing Computation (PEC) Technologies Market
- 16.4.1. Country Segmental Analysis
- 16.4.2. Technology Type
- 16.4.3. Deployment Mode
- 16.4.4. Component
- 16.4.5. Compute Architecture
- 16.4.6. Data Type
- 16.4.7. Organization Size
- 16.4.8. Application
- 16.4.9. Industry Vertical
- 16.5. United Kingdom Privacy-Enhancing Computation (PEC) Technologies Market
- 16.5.1. Country Segmental Analysis
- 16.5.2. Technology Type
- 16.5.3. Deployment Mode
- 16.5.4. Component
- 16.5.5. Compute Architecture
- 16.5.6. Data Type
- 16.5.7. Organization Size
- 16.5.8. Application
- 16.5.9. Industry Vertical
- 16.6. France Privacy-Enhancing Computation (PEC) Technologies Market
- 16.6.1. Country Segmental Analysis
- 16.6.2. Technology Type
- 16.6.3. Deployment Mode
- 16.6.4. Component
- 16.6.5. Compute Architecture
- 16.6.6. Data Type
- 16.6.7. Organization Size
- 16.6.8. Application
- 16.6.9. Industry Vertical
- 16.7. Italy Privacy-Enhancing Computation (PEC) Technologies Market
- 16.7.1. Country Segmental Analysis
- 16.7.2. Technology Type
- 16.7.3. Deployment Mode
- 16.7.4. Component
- 16.7.5. Compute Architecture
- 16.7.6. Data Type
- 16.7.7. Organization Size
- 16.7.8. Application
- 16.7.9. Industry Vertical
- 16.8. Spain Privacy-Enhancing Computation (PEC) Technologies Market
- 16.8.1. Country Segmental Analysis
- 16.8.2. Technology Type
- 16.8.3. Deployment Mode
- 16.8.4. Component
- 16.8.5. Compute Architecture
- 16.8.6. Data Type
- 16.8.7. Organization Size
- 16.8.8. Application
- 16.8.9. Industry Vertical
- 16.9. Netherlands Privacy-Enhancing Computation (PEC) Technologies Market
- 16.9.1. Country Segmental Analysis
- 16.9.2. Technology Type
- 16.9.3. Deployment Mode
- 16.9.4. Component
- 16.9.5. Compute Architecture
- 16.9.6. Data Type
- 16.9.7. Organization Size
- 16.9.8. Application
- 16.9.9. Industry Vertical
- 16.10. Nordic Countries Privacy-Enhancing Computation (PEC) Technologies Market
- 16.10.1. Country Segmental Analysis
- 16.10.2. Technology Type
- 16.10.3. Deployment Mode
- 16.10.4. Component
- 16.10.5. Compute Architecture
- 16.10.6. Data Type
- 16.10.7. Organization Size
- 16.10.8. Application
- 16.10.9. Industry Vertical
- 16.11. Poland Privacy-Enhancing Computation (PEC) Technologies Market
- 16.11.1. Country Segmental Analysis
- 16.11.2. Technology Type
- 16.11.3. Deployment Mode
- 16.11.4. Component
- 16.11.5. Compute Architecture
- 16.11.6. Data Type
- 16.11.7. Organization Size
- 16.11.8. Application
- 16.11.9. Industry Vertical
- 16.12. Russia & CIS Privacy-Enhancing Computation (PEC) Technologies Market
- 16.12.1. Country Segmental Analysis
- 16.12.2. Technology Type
- 16.12.3. Deployment Mode
- 16.12.4. Component
- 16.12.5. Compute Architecture
- 16.12.6. Data Type
- 16.12.7. Organization Size
- 16.12.8. Application
- 16.12.9. Industry Vertical
- 16.13. Rest of Europe Privacy-Enhancing Computation (PEC) Technologies Market
- 16.13.1. Country Segmental Analysis
- 16.13.2. Technology Type
- 16.13.3. Deployment Mode
- 16.13.4. Component
- 16.13.5. Compute Architecture
- 16.13.6. Data Type
- 16.13.7. Organization Size
- 16.13.8. Application
- 16.13.9. Industry Vertical
- 17. Asia Pacific Privacy-Enhancing Computation (PEC) Technologies Market Analysis
- 17.1. Key Segment Analysis
- 17.2. Regional Snapshot
- 17.3. Asia Pacific Privacy-Enhancing Computation (PEC) Technologies Market Size (Value - US$ Bn), Analysis, and Forecasts, 2021-2035
- 17.3.1. Technology Type
- 17.3.2. Deployment Mode
- 17.3.3. Component
- 17.3.4. Compute Architecture
- 17.3.5. Data Type
- 17.3.6. Organization Size
- 17.3.7. Application
- 17.3.8. Industry Vertical
- 17.3.9. Country
- 17.3.9.1. China
- 17.3.9.2. India
- 17.3.9.3. Japan
- 17.3.9.4. South Korea
- 17.3.9.5. Australia and New Zealand
- 17.3.9.6. Indonesia
- 17.3.9.7. Malaysia
- 17.3.9.8. Thailand
- 17.3.9.9. Vietnam
- 17.3.9.10. Rest of Asia Pacific
- 17.4. China Privacy-Enhancing Computation (PEC) Technologies Market
- 17.4.1. Country Segmental Analysis
- 17.4.2. Technology Type
- 17.4.3. Deployment Mode
- 17.4.4. Component
- 17.4.5. Compute Architecture
- 17.4.6. Data Type
- 17.4.7. Organization Size
- 17.4.8. Application
- 17.4.9. Industry Vertical
- 17.5. India Privacy-Enhancing Computation (PEC) Technologies Market
- 17.5.1. Country Segmental Analysis
- 17.5.2. Technology Type
- 17.5.3. Deployment Mode
- 17.5.4. Component
- 17.5.5. Compute Architecture
- 17.5.6. Data Type
- 17.5.7. Organization Size
- 17.5.8. Application
- 17.5.9. Industry Vertical
- 17.6. Japan Privacy-Enhancing Computation (PEC) Technologies Market
- 17.6.1. Country Segmental Analysis
- 17.6.2. Technology Type
- 17.6.3. Deployment Mode
- 17.6.4. Component
- 17.6.5. Compute Architecture
- 17.6.6. Data Type
- 17.6.7. Organization Size
- 17.6.8. Application
- 17.6.9. Industry Vertical
- 17.7. South Korea Privacy-Enhancing Computation (PEC) Technologies Market
- 17.7.1. Country Segmental Analysis
- 17.7.2. Technology Type
- 17.7.3. Deployment Mode
- 17.7.4. Component
- 17.7.5. Compute Architecture
- 17.7.6. Data Type
- 17.7.7. Organization Size
- 17.7.8. Application
- 17.7.9. Industry Vertical
- 17.8. Australia and New Zealand Privacy-Enhancing Computation (PEC) Technologies Market
- 17.8.1. Country Segmental Analysis
- 17.8.2. Technology Type
- 17.8.3. Deployment Mode
- 17.8.4. Component
- 17.8.5. Compute Architecture
- 17.8.6. Data Type
- 17.8.7. Organization Size
- 17.8.8. Application
- 17.8.9. Industry Vertical
- 17.9. Indonesia Privacy-Enhancing Computation (PEC) Technologies Market
- 17.9.1. Country Segmental Analysis
- 17.9.2. Technology Type
- 17.9.3. Deployment Mode
- 17.9.4. Component
- 17.9.5. Compute Architecture
- 17.9.6. Data Type
- 17.9.7. Organization Size
- 17.9.8. Application
- 17.9.9. Industry Vertical
- 17.10. Malaysia Privacy-Enhancing Computation (PEC) Technologies Market
- 17.10.1. Country Segmental Analysis
- 17.10.2. Technology Type
- 17.10.3. Deployment Mode
- 17.10.4. Component
- 17.10.5. Compute Architecture
- 17.10.6. Data Type
- 17.10.7. Organization Size
- 17.10.8. Application
- 17.10.9. Industry Vertical
- 17.11. Thailand Privacy-Enhancing Computation (PEC) Technologies Market
- 17.11.1. Country Segmental Analysis
- 17.11.2. Technology Type
- 17.11.3. Deployment Mode
- 17.11.4. Component
- 17.11.5. Compute Architecture
- 17.11.6. Data Type
- 17.11.7. Organization Size
- 17.11.8. Application
- 17.11.9. Industry Vertical
- 17.12. Vietnam Privacy-Enhancing Computation (PEC) Technologies Market
- 17.12.1. Country Segmental Analysis
- 17.12.2. Technology Type
- 17.12.3. Deployment Mode
- 17.12.4. Component
- 17.12.5. Compute Architecture
- 17.12.6. Data Type
- 17.12.7. Organization Size
- 17.12.8. Application
- 17.12.9. Industry Vertical
- 17.13. Rest of Asia Pacific Privacy-Enhancing Computation (PEC) Technologies Market
- 17.13.1. Country Segmental Analysis
- 17.13.2. Technology Type
- 17.13.3. Deployment Mode
- 17.13.4. Component
- 17.13.5. Compute Architecture
- 17.13.6. Data Type
- 17.13.7. Organization Size
- 17.13.8. Application
- 17.13.9. Industry Vertical
- 18. Middle East Privacy-Enhancing Computation (PEC) Technologies Market Analysis
- 18.1. Key Segment Analysis
- 18.2. Regional Snapshot
- 18.3. Middle East Privacy-Enhancing Computation (PEC) Technologies Market Size (Value - US$ Bn), Analysis, and Forecasts, 2021-2035
- 18.3.1. Technology Type
- 18.3.2. Deployment Mode
- 18.3.3. Component
- 18.3.4. Compute Architecture
- 18.3.5. Data Type
- 18.3.6. Organization Size
- 18.3.7. Application
- 18.3.8. Industry Vertical
- 18.3.9. Country
- 18.3.9.1. Turkey
- 18.3.9.2. UAE
- 18.3.9.3. Saudi Arabia
- 18.3.9.4. Israel
- 18.3.9.5. Rest of Middle East
- 18.4. Turkey Privacy-Enhancing Computation (PEC) Technologies Market
- 18.4.1. Country Segmental Analysis
- 18.4.2. Technology Type
- 18.4.3. Deployment Mode
- 18.4.4. Component
- 18.4.5. Compute Architecture
- 18.4.6. Data Type
- 18.4.7. Organization Size
- 18.4.8. Application
- 18.4.9. Industry Vertical
- 18.5. UAE Privacy-Enhancing Computation (PEC) Technologies Market
- 18.5.1. Country Segmental Analysis
- 18.5.2. Technology Type
- 18.5.3. Deployment Mode
- 18.5.4. Component
- 18.5.5. Compute Architecture
- 18.5.6. Data Type
- 18.5.7. Organization Size
- 18.5.8. Application
- 18.5.9. Industry Vertical
- 18.6. Saudi Arabia Privacy-Enhancing Computation (PEC) Technologies Market
- 18.6.1. Country Segmental Analysis
- 18.6.2. Technology Type
- 18.6.3. Deployment Mode
- 18.6.4. Component
- 18.6.5. Compute Architecture
- 18.6.6. Data Type
- 18.6.7. Organization Size
- 18.6.8. Application
- 18.6.9. Industry Vertical
- 18.7. Israel Privacy-Enhancing Computation (PEC) Technologies Market
- 18.7.1. Country Segmental Analysis
- 18.7.2. Technology Type
- 18.7.3. Deployment Mode
- 18.7.4. Component
- 18.7.5. Compute Architecture
- 18.7.6. Data Type
- 18.7.7. Organization Size
- 18.7.8. Application
- 18.7.9. Industry Vertical
- 18.8. Rest of Middle East Privacy-Enhancing Computation (PEC) Technologies Market
- 18.8.1. Country Segmental Analysis
- 18.8.2. Technology Type
- 18.8.3. Deployment Mode
- 18.8.4. Component
- 18.8.5. Compute Architecture
- 18.8.6. Data Type
- 18.8.7. Organization Size
- 18.8.8. Application
- 18.8.9. Industry Vertical
- 19. Africa Privacy-Enhancing Computation (PEC) Technologies Market Analysis
- 19.1. Key Segment Analysis
- 19.2. Regional Snapshot
- 19.3. Africa Privacy-Enhancing Computation (PEC) Technologies Market Size (Value - US$ Bn), Analysis, and Forecasts, 2021-2035
- 19.3.1. Technology Type
- 19.3.2. Deployment Mode
- 19.3.3. Component
- 19.3.4. Compute Architecture
- 19.3.5. Data Type
- 19.3.6. Organization Size
- 19.3.7. Application
- 19.3.8. Industry Vertical
- 19.3.9. Country
- 19.3.9.1. South Africa
- 19.3.9.2. Egypt
- 19.3.9.3. Nigeria
- 19.3.9.4. Algeria
- 19.3.9.5. Rest of Africa
- 19.4. South Africa Privacy-Enhancing Computation (PEC) Technologies Market
- 19.4.1. Country Segmental Analysis
- 19.4.2. Technology Type
- 19.4.3. Deployment Mode
- 19.4.4. Component
- 19.4.5. Compute Architecture
- 19.4.6. Data Type
- 19.4.7. Organization Size
- 19.4.8. Application
- 19.4.9. Industry Vertical
- 19.5. Egypt Privacy-Enhancing Computation (PEC) Technologies Market
- 19.5.1. Country Segmental Analysis
- 19.5.2. Technology Type
- 19.5.3. Deployment Mode
- 19.5.4. Component
- 19.5.5. Compute Architecture
- 19.5.6. Data Type
- 19.5.7. Organization Size
- 19.5.8. Application
- 19.5.9. Industry Vertical
- 19.6. Nigeria Privacy-Enhancing Computation (PEC) Technologies Market
- 19.6.1. Country Segmental Analysis
- 19.6.2. Technology Type
- 19.6.3. Deployment Mode
- 19.6.4. Component
- 19.6.5. Compute Architecture
- 19.6.6. Data Type
- 19.6.7. Organization Size
- 19.6.8. Application
- 19.6.9. Industry Vertical
- 19.7. Algeria Privacy-Enhancing Computation (PEC) Technologies Market
- 19.7.1. Country Segmental Analysis
- 19.7.2. Technology Type
- 19.7.3. Deployment Mode
- 19.7.4. Component
- 19.7.5. Compute Architecture
- 19.7.6. Data Type
- 19.7.7. Organization Size
- 19.7.8. Application
- 19.7.9. Industry Vertical
- 19.8. Rest of Africa Privacy-Enhancing Computation (PEC) Technologies Market
- 19.8.1. Country Segmental Analysis
- 19.8.2. Technology Type
- 19.8.3. Deployment Mode
- 19.8.4. Component
- 19.8.5. Compute Architecture
- 19.8.6. Data Type
- 19.8.7. Organization Size
- 19.8.8. Application
- 19.8.9. Industry Vertical
- 20. South America Privacy-Enhancing Computation (PEC) Technologies Market Analysis
- 20.1. Key Segment Analysis
- 20.2. Regional Snapshot
- 20.3. South America Privacy-Enhancing Computation (PEC) Technologies Market Size (Value - US$ Bn), Analysis, and Forecasts, 2021-2035
- 20.3.1. Technology Type
- 20.3.2. Deployment Mode
- 20.3.3. Component
- 20.3.4. Compute Architecture
- 20.3.5. Data Type
- 20.3.6. Organization Size
- 20.3.7. Application
- 20.3.8. Industry Vertical
- 20.3.9. Country
- 20.3.9.1. Brazil
- 20.3.9.2. Argentina
- 20.3.9.3. Rest of South America
- 20.4. Brazil Privacy-Enhancing Computation (PEC) Technologies Market
- 20.4.1. Country Segmental Analysis
- 20.4.2. Technology Type
- 20.4.3. Deployment Mode
- 20.4.4. Component
- 20.4.5. Compute Architecture
- 20.4.6. Data Type
- 20.4.7. Organization Size
- 20.4.8. Application
- 20.4.9. Industry Vertical
- 20.5. Argentina Privacy-Enhancing Computation (PEC) Technologies Market
- 20.5.1. Country Segmental Analysis
- 20.5.2. Technology Type
- 20.5.3. Deployment Mode
- 20.5.4. Component
- 20.5.5. Compute Architecture
- 20.5.6. Data Type
- 20.5.7. Organization Size
- 20.5.8. Application
- 20.5.9. Industry Vertical
- 20.6. Rest of South America Privacy-Enhancing Computation (PEC) Technologies Market
- 20.6.1. Country Segmental Analysis
- 20.6.2. Technology Type
- 20.6.3. Deployment Mode
- 20.6.4. Component
- 20.6.5. Compute Architecture
- 20.6.6. Data Type
- 20.6.7. Organization Size
- 20.6.8. Application
- 20.6.9. Industry Vertical
- 21. Key Players/ Company Profile
- 21.1. Accenture plc
- 21.1.1. Company Details/ Overview
- 21.1.2. Company Financials
- 21.1.3. Key Customers and Competitors
- 21.1.4. Business/ Industry Portfolio
- 21.1.5. Product Portfolio/ Specification Details
- 21.1.6. Pricing Data
- 21.1.7. Strategic Overview
- 21.1.8. Recent Developments
- 21.2. Amazon Web Services, Inc.
- 21.3. Apple Inc.
- 21.4. Cape Privacy
- 21.5. ConsenSys
- 21.6. DataFleets (LiveRamp)
- 21.7. Duality Technologies
- 21.8. Enveil, Inc.
- 21.9. Google LLC
- 21.10. HPE (Hewlett Packard Enterprise)
- 21.11. IBM Corporation
- 21.12. Inpher, Inc.
- 21.13. Intel Corporation
- 21.14. Meta Platforms, Inc.
- 21.15. Microsoft Corporation
- 21.16. Oasis Labs
- 21.17. Partisia Blockchain
- 21.18. Secret Network (SCRT Labs)
- 21.19. Snowflake Inc.
- 21.20. Zama
- 21.21. Others Key Players
- 21.1. Accenture plc
Note* - This is just tentative list of players. While providing the report, we will cover more number of players based on their revenue and share for each geography
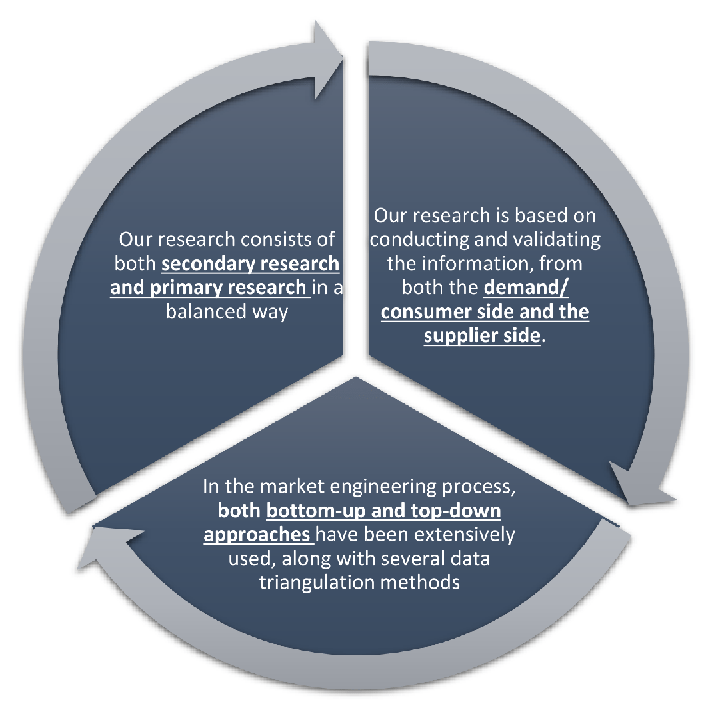
Research Design
Our research design integrates both demand-side and supply-side analysis through a balanced combination of primary and secondary research methodologies. By utilizing both bottom-up and top-down approaches alongside rigorous data triangulation methods, we deliver robust market intelligence that supports strategic decision-making.
MarketGenics' comprehensive research design framework ensures the delivery of accurate, reliable, and actionable market intelligence. Through the integration of multiple research approaches, rigorous validation processes, and expert analysis, we provide our clients with the insights needed to make informed strategic decisions and capitalize on market opportunities.
MarketGenics leverages a dedicated industry panel of experts and a comprehensive suite of paid databases to effectively collect, consolidate, and analyze market intelligence.
Our approach has consistently proven to be reliable and effective in generating accurate market insights, identifying key industry trends, and uncovering emerging business opportunities.
Through both primary and secondary research, we capture and analyze critical company-level data such as manufacturing footprints, including technical centers, R&D facilities, sales offices, and headquarters.
Our expert panel further enhances our ability to estimate market size for specific brands based on validated field-level intelligence.
Our data mining techniques incorporate both parametric and non-parametric methods, allowing for structured data collection, sorting, processing, and cleaning.
Demand projections are derived from large-scale data sets analyzed through proprietary algorithms, culminating in robust and reliable market sizing.
Research Approach
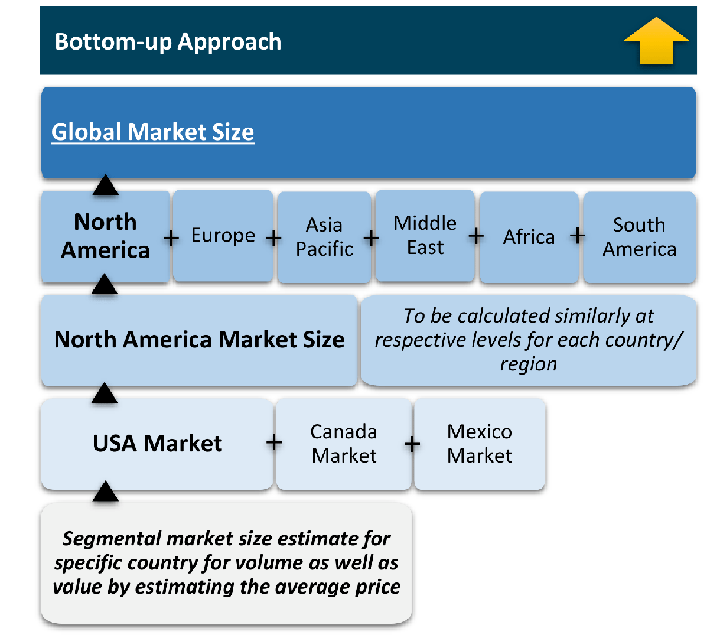
The bottom-up approach builds market estimates by starting with the smallest addressable market units and systematically aggregating them to create comprehensive market size projections.
This method begins with specific, granular data points and builds upward to create the complete market landscape.
Customer Analysis → Segmental Analysis → Geographical Analysis
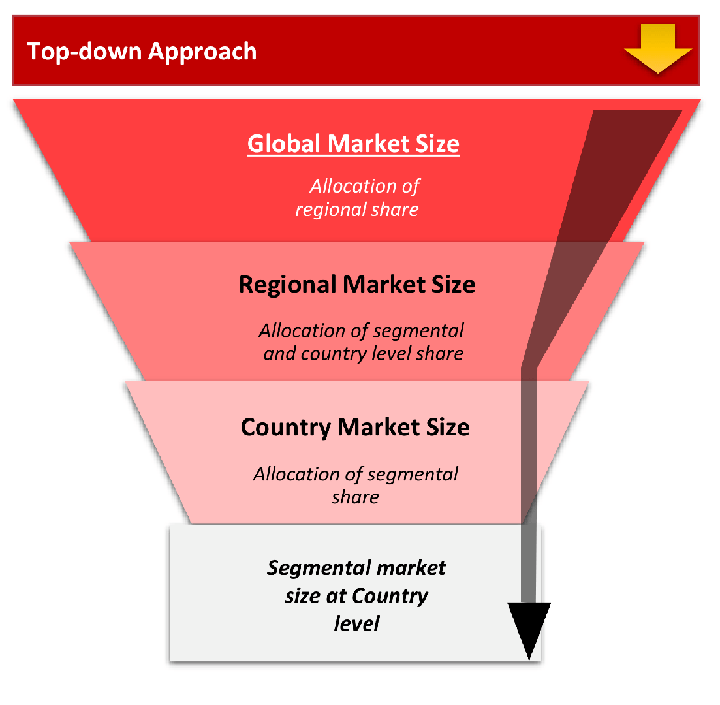
The top-down approach starts with the broadest possible market data and systematically narrows it down through a series of filters and assumptions to arrive at specific market segments or opportunities.
This method begins with the big picture and works downward to increasingly specific market slices.
TAM → SAM → SOM
Research Methods
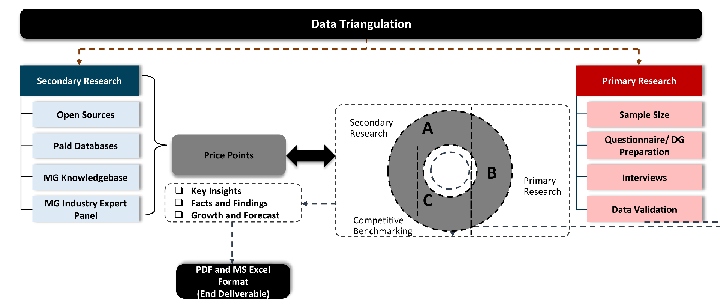
Desk / Secondary Research
While analysing the market, we extensively study secondary sources, directories, and databases to identify and collect information useful for this technical, market-oriented, and commercial report. Secondary sources that we utilize are not only the public sources, but it is a combination of Open Source, Associations, Paid Databases, MG Repository & Knowledgebase, and others.
- Company websites, annual reports, financial reports, broker reports, and investor presentations
- National government documents, statistical databases and reports
- News articles, press releases and web-casts specific to the companies operating in the market, Magazines, reports, and others
- We gather information from commercial data sources for deriving company specific data such as segmental revenue, share for geography, product revenue, and others
- Internal and external proprietary databases (industry-specific), relevant patent, and regulatory databases
- Governing Bodies, Government Organizations
- Relevant Authorities, Country-specific Associations for Industries
We also employ the model mapping approach to estimate the product level market data through the players' product portfolio
Primary Research
Primary research/ interviews is vital in analyzing the market. Most of the cases involves paid primary interviews. Primary sources include primary interviews through e-mail interactions, telephonic interviews, surveys as well as face-to-face interviews with the different stakeholders across the value chain including several industry experts.
| Type of Respondents | Number of Primaries |
|---|---|
| Tier 2/3 Suppliers | ~20 |
| Tier 1 Suppliers | ~25 |
| End-users | ~25 |
| Industry Expert/ Panel/ Consultant | ~30 |
| Total | ~100 |
MG Knowledgebase
• Repository of industry blog, newsletter and case studies
• Online platform covering detailed market reports, and company profiles
Forecasting Factors and Models
Forecasting Factors
- Historical Trends – Past market patterns, cycles, and major events that shaped how markets behave over time. Understanding past trends helps predict future behavior.
- Industry Factors – Specific characteristics of the industry like structure, regulations, and innovation cycles that affect market dynamics.
- Macroeconomic Factors – Economic conditions like GDP growth, inflation, and employment rates that affect how much money people have to spend.
- Demographic Factors – Population characteristics like age, income, and location that determine who can buy your product.
- Technology Factors – How quickly people adopt new technology and how much technology infrastructure exists.
- Regulatory Factors – Government rules, laws, and policies that can help or restrict market growth.
- Competitive Factors – Analyzing competition structure such as degree of competition and bargaining power of buyers and suppliers.
Forecasting Models / Techniques
Multiple Regression Analysis
- Identify and quantify factors that drive market changes
- Statistical modeling to establish relationships between market drivers and outcomes
Time Series Analysis – Seasonal Patterns
- Understand regular cyclical patterns in market demand
- Advanced statistical techniques to separate trend, seasonal, and irregular components
Time Series Analysis – Trend Analysis
- Identify underlying market growth patterns and momentum
- Statistical analysis of historical data to project future trends
Expert Opinion – Expert Interviews
- Gather deep industry insights and contextual understanding
- In-depth interviews with key industry stakeholders
Multi-Scenario Development
- Prepare for uncertainty by modeling different possible futures
- Creating optimistic, pessimistic, and most likely scenarios
Time Series Analysis – Moving Averages
- Sophisticated forecasting for complex time series data
- Auto-regressive integrated moving average models with seasonal components
Econometric Models
- Apply economic theory to market forecasting
- Sophisticated economic models that account for market interactions
Expert Opinion – Delphi Method
- Harness collective wisdom of industry experts
- Structured, multi-round expert consultation process
Monte Carlo Simulation
- Quantify uncertainty and probability distributions
- Thousands of simulations with varying input parameters
Research Analysis
Our research framework is built upon the fundamental principle of validating market intelligence from both demand and supply perspectives. This dual-sided approach ensures comprehensive market understanding and reduces the risk of single-source bias.
Demand-Side Analysis: We understand end-user/application behavior, preferences, and market needs along with the penetration of the product for specific application.
Supply-Side Analysis: We estimate overall market revenue, analyze the segmental share along with industry capacity, competitive landscape, and market structure.
Validation & Evaluation
Data triangulation is a validation technique that uses multiple methods, sources, or perspectives to examine the same research question, thereby increasing the credibility and reliability of research findings. In market research, triangulation serves as a quality assurance mechanism that helps identify and minimize bias, validate assumptions, and ensure accuracy in market estimates.
- Data Source Triangulation – Using multiple data sources to examine the same phenomenon
- Methodological Triangulation – Using multiple research methods to study the same research question
- Investigator Triangulation – Using multiple researchers or analysts to examine the same data
- Theoretical Triangulation – Using multiple theoretical perspectives to interpret the same data
Custom Market Research Services
We will customise the research for you, in case the report listed above does not meet your requirements.
Get 10% Free Customisation